What are the most deadly Linux commands?

• Welcome to the rogue’s gallery of lethal Linux commands.
• Many Linux commands offer no yes/no query before cheerily destroying everything that makes your life worthwhile.
• Which Linux commands should you treat like nuclear waste?
Linux, an open source, advanced operating system, is hugely popular worldwide among developers and general users. One of the reasons for its popularity is the ease with which users can run commands. Not only are running commands on the Linux terminal simple, they are also fast, typically providing a better experience when compared to using the Linux GUI (Graphical User Interface).
Users can execute Linux commands to gain access to features that are not available with a Linux GUI, but if they are inexperienced in coding, Linux systems can face some serious issues, some of which can be irreparable.
Unfortunately, many Linux beginners fall into the deadly trap of certain Linux commands. If you’re not familiar with these commands, there is a higher risk of executing a malicious command that crashes your whole system. Therefore, a thorough understanding of Linux commands is needed to avoid causing significant harm to the system and data, (known in the industry as borking or bricking).
Be very very careful and Linux will love you.
Linux commands: rm-rf
One example of a dangerous command is rm -rf / Command. The rm command, alongside different arguments, can delete files and directories. Therefore, you must be super vigilant when running this command with various options. If you’re not careful, you can potentially wave bye-bye to important files and data. It’s worth noting, however, that users who have root user privileges do not run the risk of deleting all files when executing the rm-rf/ command.
While the command rm -rf / is one instance of executing the rm command, there are additional arguments that can delete files, such as:
- -f: Deletes files within directories and files that are set as read-only, performed in a recursive manner.
- -r: Files are deleted recursively across all subdirectories, including those that are empty.
- -rf: All folders and subfolders are deleted.
The process killer: echo b
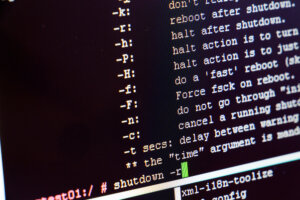
If you want to reboot your system immediately, kill processes, and unmount filesystems (we’re guessing you don’t), enter the command echo b > /proc/sysrq-trigger. That being said, this command does have some legitimate uses. For instance, if you have booted to a root shell with init=/bin/bash, but need to reboot, you can run this command – but you will need to run sync beforehand.
Linux commands – useful, but be very careful what you do.
When you execute command >/dev/sda, the output is written on the /dev/sda block (on your hard drive). A dev/sda block holds filesystem data, which gets replaced with the command output. The result? Irrecoverable damage to your system.
Short for cat /dev/null > file, the > file command allows users to redirect a command to a file. This can be highly beneficial for storing and managing the command’s output efficiently. But, if you run the command carelessly, or make a mistake in the command syntax, a critical system file can be wiped out completely.
When using the bash redirection feature, the > file command flushes the contents of a file, wiping it completely clean. For instance, running > phoenixnap.conf will result in the output creating an empty configuration file. Also, if you add a leading whitespace before the command in the bash shell, it will prevent the command from being logged, enabling someone to erase files without leaving any trace.
The crontab -r command is great for automating everyday tasks, but because all the commands are stored in a single crontab file, they are vulnerable to being removed when the -r flag is specified. Users sometimes do this by mistake when trying to specify the -e flag, but mistakenly enter -r. Bear in mind that there is no yes/no prompt before you remove the file, so you may not even know what you’ve done until it’s too late. As there are not many recovery options once you delete a crontab file, it’s best to back them up before your Homer Simpson fingers destroy your day, your files, and a good portion of your faith in humanity.
How to bork systems and have a truly terrible day
These are just a few deadly Linux commands. Here are some others to avoid:
- Chmod -R 777 / Command
- Fork Bomb command – : (){ : | :& }; :
- history | sh
- gunzip untrusted.gz
- mkfs.ext3 /dev/sda
- mv folder /dev/null Command
- gunzip untrusted.gz
- mkfs.ext3 /dev/sda Command
- chmod -R 777 /
- mv command – mv directory /dev/null
This should go without saying, and would in a species more sensible than human beings, but if you are not familiar with a Linux command, you should stay away from it. Treat it like the nuclear codes.
Avoid unreliable or unknown sources when compiling or executing files, too. The Linux commands above are known to be dangerous and deadly, so do not execute them in your Linux system or Linux VPS in any way. If you do, your Linux system may be damaged for good, and valuable data could be lost.
Don’t be that Linux-user. Nobody likes them, and they cry a lot. Practice “safe Linux” – every time.










