83% of organizations facing double, triple ransomware extortion
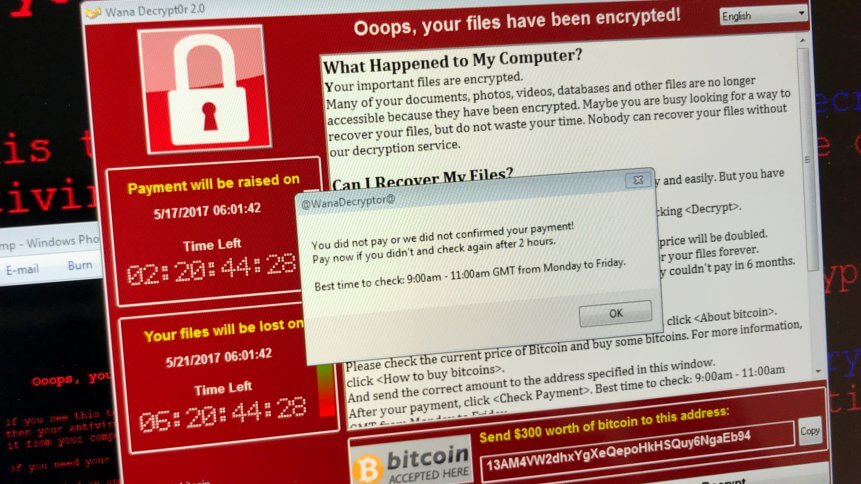
The evolution of ransomware over the last few years continues to be a huge problem for organizations. As companies invest in more cybersecurity solutions to boost their defenses and protect their data and workloads, ransomware seems to always be able to find a way around these defenses.
Spurred by their infiltration success, most ransomware operators often brazenly expertise their service on the dark web and underground forums. The rise of ransomware-as-a-service to sophistication in attack methods today includes threats of double and triple extortion to ransom demands as well. Victims are having no choice but to comply with the demands.
A Venafi survey shows that 83% of successful ransomware attacks feature double or triple extortion. Instead of just straightforward lockout or denial of access to an organization’s data, cybercriminals are now adding additional features or stages to their attacks.
Double extortion, which emerged as a trend in the first quarter of 2020, extracts sensitive commercial data before encrypting a victim’s database, according to Check Point Research. Bad actors then threaten to publish the private data to ratchet up the pressure. Triple extortion, a trend that followed suit soon after this, targets an organization’s customers or suppliers with threats to expose data that has been gathered from the victim organization.
The evolution of ransomware
Venafi’s report also showed that 83% of successful ransomware attacks over the past year have featured double or triple extortion. 71% of ITDMs (IT Decision Makers) also believe the practice is more common than it was 12 months ago. A further breakdown of data shows these new forms of ransomware — such as those extorting customers — are becoming more common, according to Venafi’s data on attack schemes.
With ransomware attack methodologies evolving faster than security controls, the additional pressure exacted by double or triple extortion makes it harder for organizations to reject demands.
- 72% agree that ransomware attacks are evolving faster than the security controls needed to protect against them
- As a result, 76% of companies are planning on spending more in 2022 on ransomware-specific controls due to the threat of double/triple extortion
- 65% agree that double or triple extortion demands make it much harder to say no to ransom demands
But despite this increased pressure:
- 75% agree that companies that pay ransoms are soft targets for future attacks
- 74% agree that paying a ransom for any attack is bad for everyone because it fuels the ransomware ecosystem
“It is very easy and quick for ransomware developers to add new exploits or capabilities to their malware. Every new exploit for a vulnerability that is exposed online can be used within a few days by ransomware developers in their attacks,” said Yana Blachman, Threat Intelligence Analyst at Venafi.
Blachman added that for defenders, on the other hand, security controls are much harder to implement because it can take weeks or months to respond with patches and new controls.
At the same time, Blachman also pointed out that cybercriminals often get their hands on sensitive and private data that perhaps the whole business relies on. They also understand that organizations have implemented recovery systems and backups, now that ransomware is practically everywhere, and this is their best shot at getting their targets to pay.
Dealing with double or triple extortion ransomware
More than three-quarters of those surveyed say governments need to step in and help companies combat ransomware and that companies and governments need to work together.
- 67% agree that public reporting of ransomware attacks and ransom payments will slow down the growth of ransomware
- 74% agree that ransomware should be considered a matter of national security
- 77% agree that governments need to do more to help private companies defend themselves from ransomware going forward
- And 76% agree that moving forward, companies and governments need to work more closely together to tackle the threat of ransomware
The U.S. government has become more proactive in its efforts to combat ransomware. For example, the Cybersecurity Infrastructure and Security Agency (CISA) is devoted to providing best practices to mitigate the chances of a ransomware attack. The CISA continues to release advisories together with other government agencies both locally and internationally on dealing with ransomware.
But that doesn’t mean ransomware is going to conveniently fade away. For Eddie Glenn, Senior Product Marketing Manager at Venafi, there is no single way to tackle ransomware. Glenn said methods such as preventing links from being clicked on in the email, email attachments from being sent, or macros being run within spreadsheets haven’t been effective.
“An easy thing that a company can do is to require all macros to be signed with a company- security-policy-approved code signing certificate that has been issued to an individual. This way the person receiving the macro can be assured that the macro originated with the trusted employee and not a malicious external third party,” Glenn mentioned.
Glenn also highlighted that adopting more modern security practices, like code signing macros or a Zero Trust security model, can address these threats with minimal hit on efficiency.









