Barracuda ESG hack one of the ‘best’ of 2023

|
Getting your Trinity Audio player ready...
|
The events surrounding a hack in computer circles contribute to whether they’re remembered, in addition to their scope, the numbers of people affected negatively, or the amount of data exfiltrated by the bad actors behind the events.
Many data breaches seem to be no more than 5-minute hacks that happened to get lucky, while others, such as the campaign around the 2016 US presidential election and the Ukrainian power blackouts, are – allegedly – the work of state-sponsored groups that represent months of planning and work. Cybersecurity specialists often have a grudging respect for their adversaries: it takes an expert to recognize a fellow craftsman.
Hacking techniques range in complexity and the skill and forethought put into the methods used. On the one hand, there are the chancers whose techniques are pretty basic but likely to yield some success from any targets found that have little or no cybersecurity. At the other end of the spectrum are the outfits that produce well-written code that follows an obviously planned series of processes, the whole redolent of months of intensive work by bad actors who know exactly what they’re doing.
Great Barracuda off the Netherland Antilles.jpg” by The original uploader was Aquaimages at English Wikipedia. is licensed under CC BY-SA 2.5.
The recent attack on Barracuda’s Email Security Gateway devices (ESG) was definitely one of the latter. It was so effective, in fact, that Barracuda’s final response (after failed attempts to patch the security flaws) was to inform its customers to simply scrap the devices altogether.
While the extent of the effects on the compromised devices is still being measured, it’s likely to be an event that sticks in the mythos thanks to its complexity and, for want of a better word, cleverness. It was an attack that was impressive in its execution, thanks to how the instances of malicious code kept themselves persistent and the obvious effort that the bad actors had gone to test their outcomes and ensure maximum efficiency. They also targeted a device responsible for processing and filtering huge amounts of emails, one that additionally isn’t necessarily connected directly to the internet.
It was a highly targeted attack, but not necessarily targeted at a particular institution, nor should “targeted” give the impression that few devices were compromised. In fact, by taking control of large numbers of devices commonly deployed in enterprise settings, the bad actors were able to intercept entire conversations (surrounding negotiations between nation states, it is thought). Plus, the hackers gained access to huge amounts of intellectual property and – to add insult to injury – used their strongholds inside organizations’ infrastructure to move sideways onto other targets.
Forensic teams have yet to fully understand quite how far this breach went, but given that it probably landed on victims’ devices in October 2022, there have been at least eight months of illicit activity emanating from Barracuda’s Email Security Gateways. And the planning and coding for this breach will have taken months in the execution.
The worst hacks in computer history
The term “severe” in cybersecurity means different things, according to context. A severe vulnerability may not ever have led to anything exploiting it, and the effects of a severe incident may only be felt by a few people in a single institution or body. When mainstream media terms an incident “severe,” it likely means that there are thousands of affected parties, each of whom may be in danger of data loss, identity theft, financial loss, or public humiliation.
To reach mainstream attention, the affected organizations have to openly admit their victimhood, which a surprising number decline to do. Breaches are either not mentioned at all, denied, played down, or only admitted to some time after the event.
The chances are good, then, that we’ve never heard about some of the worst hacks in computer history. But of those that are in the public domain, as it were, notable recent examples are:
- Petya and Notpetya affected Ukrainian infrastructure, the Chernobyl ex-nuclear plant’s monitoring systems, shipping giant Maersk Line, pharma company Merck, DHL, and many more, with a White House assessment putting the total damage to around $10bn by 2018.
- The compromise of SolarWinds Orion software in 2020 showed how the breach of a cybersecurity firm’s assets could, in turn, cross-infect many of its clients. A class action lawsuit by affected parties finally settled in 2022, but not after a legal battle where accusations of insider trading came to light – stock offloads by staff aware of the breach before it was made publicly known.
- The Shadow Brokers hacking group most famously hacked the NSA in 2016 and was pegged as acting on behalf of the Russian state. Shady Russian figures are also said to have been behind the SolarWinds breach and notpetya and petya ransomware.
- Earlier still, the US Office of Personnel Management was breached multiple times in 2013 and 2014 by malicious parties said to be of Chinese origin. Personnel records for current and ex-federal employees were exfiltrated in this case, including fingerprint records.
The carefully developed attack on the Barracuda Email Gateway is thought to have been perpetrated by Chinese state-backed hackers. Certainly, the project will have been worked on for many months before the vulnerability in the devices came to light in October 2022. It’s safe to assume, therefore, that the group discovered the susceptibility many months prior and were well-resourced throughout the project.

Malware presented as Lua scripts extending the Barracuda ESG. Source: Twitter
Anatomy of an attack
Hackers sent emails carefully modeled as spam to addresses in front of the Barracuda Email Gateways with an attachment comprising a compressed archive. By default, the device would unpack the archive to scan its contents for malicious code.
One of the files in the archive was named with the verbatim exploit code, which the device would have parsed. To simplify this explanation, imagine sending a file called “shutdown this laptop.docx” to someone whose laptop immediately shut down on receiving it.
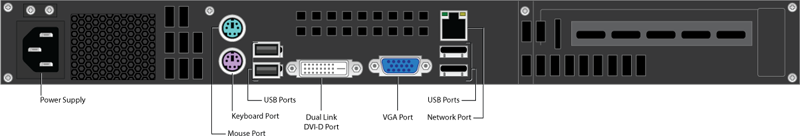
The port marked “Ethernet” is where the malware instances entered. Source: Barracuda
In actual fact, the malicious code opened a connection to online assets owned by the group, which now had root-level access to the compromised device.
By taking its place in a list of clearly spam emails, the malicious message gained a huge degree of camouflage: hiding in plain sight, where the majority of scanners, both human and automatic, would ignore it. Once the ESG was compromised, therefore, it would be unlikely that the corrupting email would be obvious.
What sets the attack apart is the range of belt-and-braces steps the attackers then took to ensure the persistence of their code. The malware established periodic checks (cron jobs) to ensure their entities had been deleted, plus they crafted email scanning plugins that worked alongside the still-functioning ESGs that would also check that the malware had been deleted.
Code was also deployed into the compromised devices’ startup routines to check at boot time to see if the malware was still present and, if not, reinstate it. It’s easy to imagine the bad actors ‘workshopping’ the various scenarios in which they would be thwarted, and coming up with solutions to circumvent any steps taken.
Once securely in place, access to all the emails that ran through an organization’s Barracuda ESG could be exfiltrated, scanned, filtered, or doctored by the attackers.
There is also some evidence that the group used the compromised machines as a base for further infiltration to other devices on the organization’s network.
YOU MIGHT LIKE

It’s not just Windows that gets malware
The aftermath of this hack in computer mythology
At some stage, after it had realized its devices had been affected at a significant scale, Barracuda reached out to the Google cybersecurity experts at Mandiant, whose report on the incident gives a great deal more technical detail than this article could contain.
After issuing patches to customers of the ESG, Barracuda soon noted that compromised devices were quickly reinfected. Thus it suggested to all its users that the device be taken offline.
Email’s ubiquity has always made it a popular target among hackers, but email-based attacks usually need human interaction: a user clicking a link or attachment. In this case, the affected devices were compromised by an email payload that needed no human action.
Given that an email’s journey from sender to recipient may pass through several devices en route (load balancers, IDSs, malware scanners, relays, quarantine storage, etc.), an organization’s attack surface suddenly looks much wider than previously imagined. A compromised security device, even one carefully VLANed away from the outside world, can wreak havoc and literally contribute to e-waste.
YOU MIGHT LIKE










