It’s not just Windows that gets malware
|
Getting your Trinity Audio player ready...
|
It’s accepted as a given that running Windows software means staying vigilant to protect against malware attacks. Frequent security scans are all part of the Windows experience, so says the ever-so-slightly smug MacOS user who can’t imagine how awful a susceptibility to hacking must be.
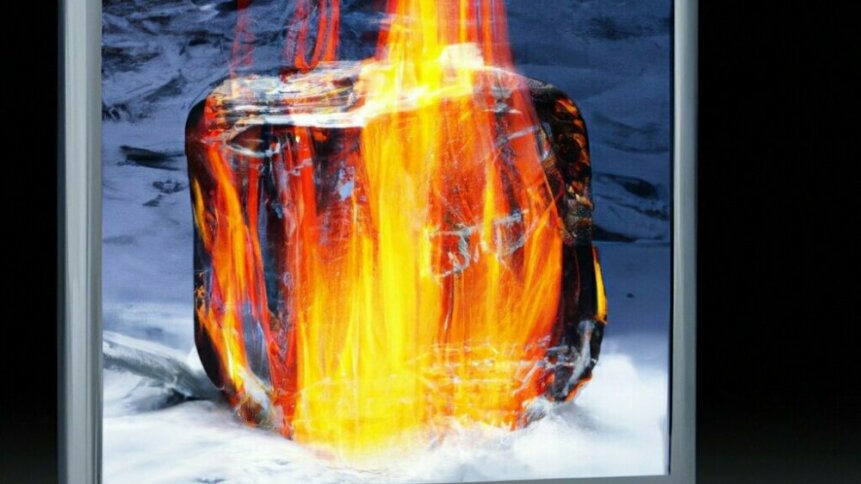
There’s a mythologized idea that Apple’s MacBooks are immune to to malware — so, you clever consumers with deeper-than-average pockets needn’t worry about system security.
To state the obvious: that’s not true. If you aren’t going to preventatively protect against malwareware, it’s best not to use your MacBook in ways that essentially invite it in. For example, the $300 that Final Cut Pro costs might make downloading a large pirated file from a torrent appealing, especially with the false confidence of using not-a-Windows-PC.
Security researchers at Jamf have found that torrents on The Pirate Bay, claiming to contain Final Cut Pro are instead distributing cryptojacking malware to Macs. On installation of the pirated version of “Final Cut Pro”, users will see a message saying that the file is damaged and can’t be opened. Behind the scenes, the Mac is covertly mining cryptocurrency on behalf of cybercriminals, using up CPU cycles.
Traditionally adware was the most widespread type of MacOS malware, but as Apple’s ARM processors continue to advance, they’ll get more attractive for crypto-mining, which will benefit from high processing power.
Part of the reason why this malware has been so successful could be psychological. As well as the false sense of security that Apple marketing encourages, users won’t be surprised when the download seemingly doesn’t work — of course the hyper-secure MacOS wouldn’t allow the illegal download of a free version of one of its more commonly-used applications.
This leaves the malware to run behind the scenes; if the user does realise that they’ve downloaded ransomware, they’re unlikely to be honest with security and IT teams about how it got there.
Everyone must protect against malware
The bad actor responsible for the poisoned Final Cut Pro torrents has uploaded numerous other malicious payloads that mine cryptocurrency, and has been doing so since 2019. Many of the malware packages are among the most widely shared versions of their respective titles.
Historically, Windows has been low-hanging fruit for bad actors. However, as the processing power of Apple begins to draw their attention, so too is the mass-usage of Linux making it an appealing target.
Compared to Windows, Linux is more difficult to infiltrate with ransomware, especially at scale. Typical infection vectors like phishing or drive-by download aren’t effective, because most Linux systems in productions are headless servers (run without a traditional desktop where users interact with the system). Often, the feat of taking on Linux seemed pointless with Windows being such an easy target.
However, the world increasingly runs on Linux. A major takedown of the server stands to have massive impact, and hacks are beginning to hit it. Bad actors are exploiting application vulnerabilities, as demonstrated by IceFire, who have previously focused only on attacking Windows.
Linux versions of IceFire ransomeware have been found to have intruded on several media and entertainment sector organizations worldwide. Observations currently indicate that the attackers deployed the ransomware by exploiting CVE-2022-47986, a deserialization vulnerability in IBM Aspera Faspex file sharing software.
The hack sees IceFire drop a ransom note from an embedded resource in the binary, written to each directory targeted for file encryption. It contains a hardcoded username and password that are required to log in to the ransom payment portal hosted on a Tor-hidden service.
Traced to the group because the Linux version’s Onion hostname matches the hostname that ransomware trackers tie to IceFire, including attacks targeting Windows, the evolution shows the increasing popularity of ransomware targeting Linux for 2023.
Long-term Windows users may be able to sit back with some satisfaction as previously “immune” software comes under new fire. They shouldn’t get too comfortable, however. As long as the Windows desktop predominates, soo too will the number of malware instances that target the platform.








