Cisco: Employee’s credentials compromised by sophisticated voice phishing attacks

- Through a series of sophisticated voice phishing attacks, threat actors hijacked a Cisco employee’s personal Google accounts, convincing them to accept multi-factor authentication (MFA) push notifications.
- Cisco experienced a security incident on their corporate network in late May 2022, and claimed to have immediately taken action to contain and eradicate the bad actors.
Just last month, a new report by Mutare revealed serious shortcomings in enterprise security protections against voice network attacks. The report highlighted that nearly half (47%) of the organizations surveyed had experienced a vishing (voice phishing) or social engineering attack in the past year. Network giant Cisco Systems Inc recently became a victim itself, which eventually led to employees’ credentials being compromised.
The California-based company said in a blog post published on Wednesday that an investigation had determined that a hacker broke into Cisco’s network by cracking into an employee’s personal Google account, which synchronized their saved passwords across the web. Cisco became aware of a potential compromise on May 24, and disclosed it this week after the hacker leaked a list of the files they had stolen on the dark web.
Investigators believe that the attack was conducted by an adversary who has previously been identified as an initial access broker for several notorious cybercrime groups: UNC2447, Lapsus$ and Yanluowang ransomware operators. Initial access brokers attempt to gain privileged access to corporate computer networks and then sell it to other hackers.
How was the voice phishing attacks carried out?
Cisco’s blog post suggests that the Yanluowang threat actors gained access to Cisco’s network using an employee’s stolen credentials after hijacking the employee’s personal Google account. That account contained credentials synced from their browser. The attacker then convinced the Cisco employee to accept multi-factor authentication (MFA) push notifications through MFA fatigue and a series of sophisticated voice phishing attacks initiated by the Yanluowang gang that impersonated trusted support organizations.
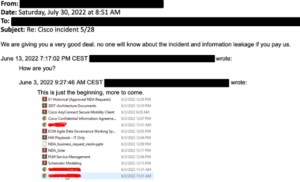
The adversary redacted the directory listing screenshot prior to sending the email.
Source: Cisco
Finally, the threat actors tricked the victim into accepting one of the MFA notifications and gained access to the VPN in the context of the targeted user. Once they gained a foothold on the company’s corporate network, Yanluowang operators spread laterally to Citrix servers and domain controllers. “They moved into the Citrix environment, compromising a series of Citrix servers, and eventually obtained privileged access to domain controllers,” Cisco Talos said.
After gaining domain administrator privilege, threat actors used enumeration tools like ntdsutil, adfind, and secretsdump to collect more information and installed a series of payloads onto compromised systems, including a backdoor. When Cisco detected it, the actors were immediately evicted from its environment, but they continued trying to regain access over the following weeks.
“After obtaining initial access, the threat actor conducted a variety of activities to maintain access, minimize forensic artifacts, and increase their level of access to systems within the environment,” Cisco Talos added. “The threat actor was successfully removed from the environment and displayed persistence, repeatedly attempting to regain access in the weeks following the attack; however, these attempts were unsuccessful.”
The upside is that Cisco has “not identified any evidence suggesting that the attacker gained access to critical internal systems, such as those related to product development, code signing, etc.,” according to the blog. “The only successful data exfiltration that occurred during the attack included the contents of a Box folder that was associated with a compromised employee’s account. The data obtained by the adversary in this case was not sensitive.”
In a twist of events however, the threat actor behind the Cisco hack emailed BleepingComputer a directory listing of files allegedly stolen during the attack. The threat actor claimed to have stolen 2.75GB of data, consisting of approximately 3,100 files. Many of these files are non-disclosure agreements, data dumps, and engineering drawings. The threat actors also sent a redacted NDA document stolen in the attack to BleepingComputer as proof of the attack and a “hint” that they breached Cisco’s network and exfiltrated files.










