Is the US setting the pace for quantum computing in cybersecurity?

Quantum computing algorithms is most likely going to be the future of cybersecurity. US President Joe Biden recently signed a National Security Memorandum (NSM) aimed at maintaining U.S. leadership in quantum information sciences and mitigating the risks of quantum computing to the nation’s security. The NSM will direct US government agencies to migrate vulnerable cryptographic systems to quantum-resistant cryptography.
The National Institute of Standards and Technology (NIST) will also publish new quantum-resistant cryptographic algorithms that can protect against future cyberattacks. These “quantum-resilient cryptographic standards” being developed by NIST will be vital to ensure the future of secure communications on the internet, officials explained.
“However, the process to transition America’s most vulnerable IT systems to these new standards will take time, resources, and commitment. America must start the lengthy process of updating our IT infrastructure today to protect against this quantum computing threat tomorrow,” according to a fact sheet by the Biden Administration.
As government agencies migrate, what will this mean for enterprises in the US? And how will this impact the development of quantum computing in the future? Will organizations now have to add additional quantum-based security systems to protect their data from cybercriminals?
The quantum journey
To understand more about this, Tech HQ speaks to Duncan Jones, head of cybersecurity at Quantinuum, the world’s first full-stack quantum computing company.

Duncan Jones, Head of Cybersecurity at Quantinuum.
According to Jones, Biden’s announcement has been encouraging the right level of focus on the migration that is needed to be quantum secure. He added the latest memo focuses on the need to be prepared and prioritized and a holistic approach to having the quantum skillset needed for the future.
Jones also explained that the use of quantum computing in cybersecurity ensures the work done is safe and organizations’ data not being targeted by nation-states. However, Jones felt that while organizations and government agencies look to migrate to quantum computing cybersecurity, cybercriminals could also leverage quantum technologies in the future for their benefit.
In fact, a study by Dimensional Research showed that two-thirds of cybersecurity leaders and experts believe that current encryption protocols stand no chance against hackers using a quantum computer. The alarming part is that more than 50% of organizations are not even aware of quantum security threats, while some companies are already preparing and budgeting against quantum threats.
As such, while it may be some time before the use of quantum in cybersecurity becomes mainstream, Jones pointed out that it’s a big undertaking for organizations, especially large enterprises and government agencies.
“It’s a big undertaking. For small and medium-sized businesses, they just need to wait for their vendors to make the changes for them. But for larger organizations, government agencies, and such, there is a lot to be done. They need to understand what data is valuable and worth protecting. They need to know what cryptography is being used. Knowing this is a big task is planning the migration.
Cryptography is everywhere today. Companies need to think about how they migrate from vulnerable to quantum-safe systems. These memos make it crystal clear that the US government understands that and wants enterprises and agencies to get on with it,” commented Jones.
Adopting quantum cybersecurity
“Apart from a few examples, we are in testing phases. We are still waiting for standardized algorithms to approach this. NIST has been working on this for six years. It should be anytime now when they announce it. But even with the announcement, it takes organizations about 18 months of refinement,” added Jones.
Interestingly, sensible companies have already started experimenting with the technology. Jones mentioned that they are already doing the hard work to be ready and understand their data. For them, once the algorithms have been standardized by 2024, they will have more adoption.
“Quantinuum spends a lot of time talking about this. We use quantum for a different purpose We see it as a tool to strengthen things. We help organizations embrace quantum tech to prepare against cyberthreats,” added Jones.
One company that has been working with Quantinuum is PureVPN. Using Quantinuum’s cyber platform, Quantum Origin, PureVPN has been able to create and deploy encryption keys that are generated using a verifiable quantum process, which is more secure than keys from unverified, classical processes.
While quantum computers will be able to break traditional encryption methods, quantum-resistant technologies offer a solution, and the encryption keys are one part of the puzzle. In addition to strengthening its keys, PureVPN is progressing a transitional plan to quantum-resistant algorithms, which are currently going through an approval process by NIST. Once this has been defined, this will be the next step in their quantum journey.
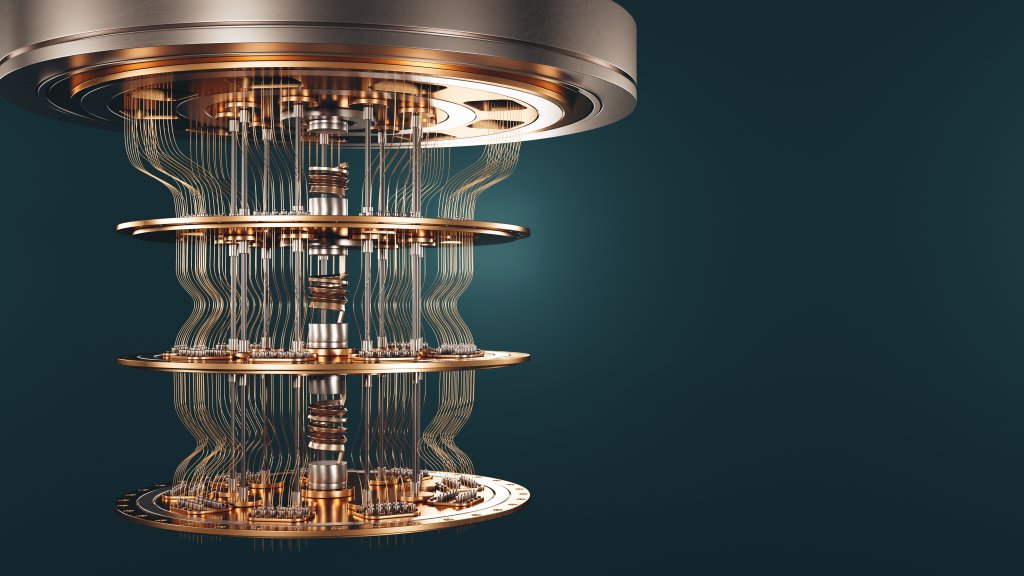
(Source – Shutterstock)
A new era in cybersecurity
For Jones, the quantum keys, regardless of the algorithms used, are highly unpredictable. Quantinuum uses quantum tech to solve this problem and help businesses in these experiments. They generate a key using a quantum origin product, which is also the first commercial product that uses a quantum computer to generate cryptographic keys. Some businesses use their products to do experimentation with algorithms.
“In cybersecurity, you rarely get a big step change in tech. Since we announced in December 2021 that we figured out how to tap into quantum with encryption keys, we have a number of ongoing opportunities with large banks, energy companies, and such, all looking to protect their data,” said Jones.
At the same time, Jones also highlighted that for organizations to embrace quantum computing in cybersecurity, they do not need to buy a quantum computer. Companies like Quantinuum provides it as a SaaS that can be integrated into existing systems, meaning businesses need not worry about high price tags.
YOU MIGHT LIKE

Getting ahead and winning the quantum talent race
“We knew we won’t be successful if we required customers to replace all their security with our stuff. If you have an existing system, you have already invested a lot in the infrastructure. We will plug into that. We take the existing system and make encryption keys stronger. Once fully converted, it will be a one-time integration. From there, we follow the company as they take their quantum security journey,” Jones explained.
Moving forward, Jones believes there are two phases enterprises should look into to ensure they are well prepared to adopt the new changes. First, which most companies can already begin implementing is to start making migration plans and understating what sensitive data and information they have. They can use quantum to generate stronger encryption keys, which are already available in the market.
The second phase is where enterprises use quantum to move these keys around safely. This is called quantum key distribution and is still in its research phase. Jones believes that it should be ready in about three to five years or even longer. Once it is ready, it can be adopted by banks and government agencies as another layer of security.









