Lapsus$ targets big organizations as Microsoft, Okta fall victim

The Lapsus$ hacker group is beginning to be a big problem for organizations around the world. The hacker group, which has a strong social media presence on Telegram focuses exclusively on data theft and extortion.
The hacker group claims to have infiltrated several large organizations. Among the organizations impacted in the last few months include Samsung, NVIDIA, and even Verizon. The group often posts screenshots of their activities on their Telegram group and even asks followers to vote on which data they should expose.
In its latest hack, Lapsus$ claims to have infiltrated two big organizations, Microsoft and Okta. Lapsus$ posted screenshots of Okta’s internal information to its Telegram channel. The group claims to have gained access to Okta’s backend systems for several months.
“After a thorough analysis of these claims, we have concluded that a small percentage of customers – approximately 2.5% – have potentially been impacted and whose data may have been viewed or acted upon. We have identified those customers and are contacting them directly,” commented David Bradbury, Chief Security Officer of Okta.
The scope of the hack is unknown but gaining access to Okta’s internal systems could enable the group to target a broad range of companies using Okta’s services. This would include businesses, universities, and government agencies that depend on Okta to authenticate their user access for internal systems.
“Thousands of companies use Okta to secure and manage their identities. This means in practice that Okta manages vast amounts of users globally. Compromises of this magnitude can have a severe impact globally and create a chain reaction in enterprises in which the identities of their employees and contractors are potentially compromised,” commented Lotem Finkelsteen, Head of Threat Intelligence and Research at Check Point Software.
Fikelsteen added that through private keys retrieved within Okta, the cyber gang may have access to corporate networks and applications. Hence, he believes a breach at Okta could lead to potentially devastating consequences which are still to be seen or exposed at this point. How the group managed to breach these targets has never fully been clear to the public. If true, Fikelsteen believes the breach at Okta may explain how Lapsus$ has been able to achieve its recent string of successful intrusions.
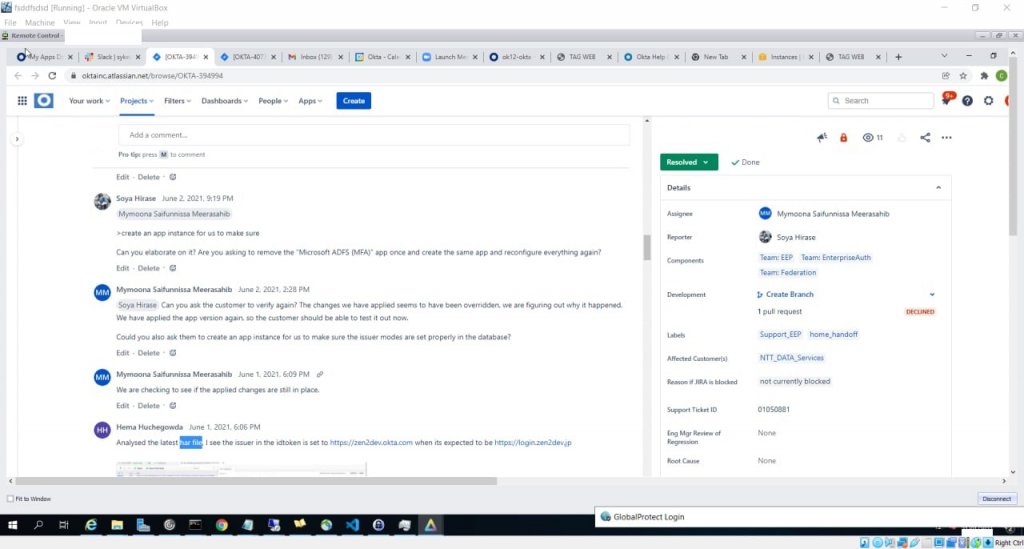
Screenshot from Lapsus$ Telegram group on access to Okta.com Superuser/Admin and various other systems. (Source – Lapsus$ Telegram)
Meanwhile, the hacking group also claims to have leaked the source code for Bing, Cortana, and other projects stolen from Microsoft’s internal Azure DevOps server. Microsoft has confirmed that Lapsus$ hackers stole their source code via limited access. Microsoft also said that the leaked code is not severe enough to cause an elevation of risk status and that its response teams shut down the hackers’ mid-operation.
“The activity we have observed has been attributed to a threat group that Microsoft tracks as DEV-0537, also known as LAPSUS$. DEV-0537 is known for using a pure extortion and destruction model without deploying ransomware payloads,” said Microsoft’s Threat Intelligence Center in its security blog post.
On its source code breach, Microsoft added that it “does not rely on the secrecy of code as a security measure and viewing source code does not lead to elevation of risk. The tactics DEV-0537 used in this intrusion reflect the tactics and techniques discussed in this blog. Our team was already investigating the compromised account based on threat intelligence when the actor publicly disclosed their intrusion. This public disclosure escalated our action allowing our team to intervene and interrupt the actor mid-operation, limiting broader impact.”
A common problem?
For Kevin Bocek, Vice President of Security Strategy and Threat Intelligence at Venafi, the attacks targeting software builds are becoming more common for several reasons.
“Firstly, hitting one target opens the door to multiple targets. Secondly, security and development teams are often not working in unison, leaving developer environments poorly defended. Yet perhaps even more worrying is that once a developer environment is compromised it is extremely difficult to remediate,” said Bocek. “That kind of access gives threat actors the keys to the kingdom, so it’s easy to maintain persistence. So, it’s no surprise we keep seeing attacks of this nature.”
Bocek also pointed out that what makes this more disturbing is that so many businesses are dependent on one human identity provider, putting all their eggs in one basket. This means if there is one breach, it opens the kimono putting multiple businesses at risk of future attacks.
“Looking at Lapsus$ specifically, they have a history of abusing machine identities and using their understanding of developer environments to their advantage. This puts the very system of trust that enables machines to communicate and software to run into jeopardy. As these types of attacks become more common, it’s vital that approaches to securing build pipelines adapt,” Bocek added. “We can’t have development teams that work with no involvement from security, equally, we cannot expect security to understand the intricacies of dev environments. We need a new breed of security developer that can bridge the gap and enable security at speed.”
Can Lapsus$ be stopped?
Microsoft suggested organizations enable multifactor authentication (MFA) as it is one of the primary lines of defense against Lapsus$. While this group attempts to identify gaps in MFA, it remains a critical pillar in identity security for employees, vendors, and other personnel alike.
Microsoft also reminded organizations to strengthen and monitor cloud security posture. Lapsus$ leverages legitimate credentials to perform malicious actions against customers. Since these credentials are legitimate, some activity performed might seem consistent with standard user behavior.
“We advise organizations to follow very tight operational security practices when responding to an intrusion believed to be DEV-0537. Organizations should develop an out-of-band communication plan for incident responders that is usable for multiple days while an investigation occurs, documentation of this response plan should be closely held and not easily accessible,” added Microsoft.
At the same time, another issue is compromised machine identities that lead to source code leaks. Pratik Selva, Senior Security Engineer at Venafi explained that attackers have abused machine identities to establish hidden or concealed encrypted communication channels and gain privileged access to data and resources. This and countless incidents highlight the need for a threat model where risks to source code need to be evaluated as a serious security risk.
Jonathan Knudsen, Senior Software Strategist, Synopsys Software Integrity Group added that organizations of all types must recognize that software risk is a business risk and take appropriate action. For Knudsen, managing software risk means including security at every stage of the software supply chain, everything from a concept through to the people or systems that use an application. But even with the best possible defenses, some attacks will always be successful. Incident response along with business continuity plans and execution are just as important as defensive measures.
“Based on the scope and frequency of attacks, Lapus$ appears to be a well-resourced organization, likely backed by organized crime or a nation-state. While the software has brought transformative power to all industries, risk must be managed properly. Enterprises should take note of recent skullduggery and adjust their priorities and processes to drive software supply chain risk to tolerable levels,” said Knudsen.”










