Securing the hybrid work place starts with browser security
Securing the hybrid work place is essential for the modern workforce in post-pandemic times. While some organizations have allowed their employees to continue working remotely, many are now requesting their vaccinated employees to return to the office in a rotation style with their colleagues, making for a hybrid working environment.
However for organizations to practice this model, they first need to ensure they create a hybrid work place environment for their employees. This includes ensuring hybrid employees are able to adapt to both working environments without disrupting their productivity. Learning from the lessons of remote work during the pandemic, most organizations now want to ensure their workforce is fully prepared to work in any environment.
When remote work was enforced, most organizations had to let employees use their own devices for work. And this led to several security issues, especially in the devices and networks being used by remote employees being vulnerable to cyberattacks.
To ensure the hybrid work place is secured, most companies would now be providing secured devices to hybrid employees to use for work. These devices would normally be patched with the latest security protection from the company’s IT team. Yet, despite this, some employees still end up having their devices infiltrated by cybercriminals.
One of the reasons for this is browser attacks. While the hybrid work place may have secured devices, browsers used by employees are often vulnerable to cyberattacks. In fact, over the past year, it has been made glaringly clear that browsers are one of the most vulnerable parts of endpoint security, putting potentially billions of users at risk for cyberattacks.
For the workforce, remote or hybrid, this creates a perfect opportunity for cybercriminals to hack into a browser and acquire confidential data. For example, the Chrome web browser by Google, which has over 2.65 billion users, continues to face security threats in recent months. Security experts believe that hackers are easily exploiting insidious zero-days, as firms are not doing a good job of permanently shutting down flaws and loopholes.
At the same time, according to IBM Security’s 2021 Cost of a Data Breach Report, the average cost for a US data breach in 2021 is US$9.05 million, up from $8.64 million in 2020. The same study also showed that it takes a company an average of 287 days to identify and contain a data breach.
To understand more about web browser-based attacks and how organizations can create a secure hybrid work place and protect both employees and their data, TechHQ speaks to Ofer Ben Noon, CEO and co-founder of Talon Cyber Security.
Are remote/hybrid working employees a weak link to browser attacks? Should enterprises relook into BYOPC policies?
The rise of hybrid working over the past 18 months has introduced serious risks to companies and their information. With employees operating from anywhere, occasionally using non-corporate endpoints, and many times using the same device and browser for both professional and private use, browser-based activities have become seriously vulnerable to attacks.
Given security systems are weaker outside of the corporate perimeter, cybercriminals have seen hybrid working – particularly the kind done on SaaS and accessed mainly through the browser – as an opportunity. Enterprises operating with BYOPC policies should make sure that they put the right security mechanisms in place to enable maximum productivity and privacy, without having to expose the organization to major cyber threats. But it’s not only BYOPC that is a concern; the browser has become the new workspace for many employees in the hybrid work era and as such, it must be properly secured.
What do security executives need to know about browser vulnerabilities, and how to protect against them?
Today, many employees spend most of their workday in the browser, making it the main entry point to the corporate environment and a lucrative target for attackers. Attacks on the distributed workforce via the browser, infiltrate using a variety of methods including zero-days targeting browser vulnerabilities, malware on the endpoint, malicious extensions, fraudulent emails, and phishing attempts.
The browser, which is ultimately a consumer-based application, traditionally lacks the security controls offered by corporate-oriented applications that are connected with a security backend management, and therefore, may compromise the corporate environment. Companies can protect against these risks by implementing solutions that ensure data security, full visibility, and control. This means creating a secure environment that is endpoint-agnostic, easy to operate, and has a consistent security posture for all endpoints.

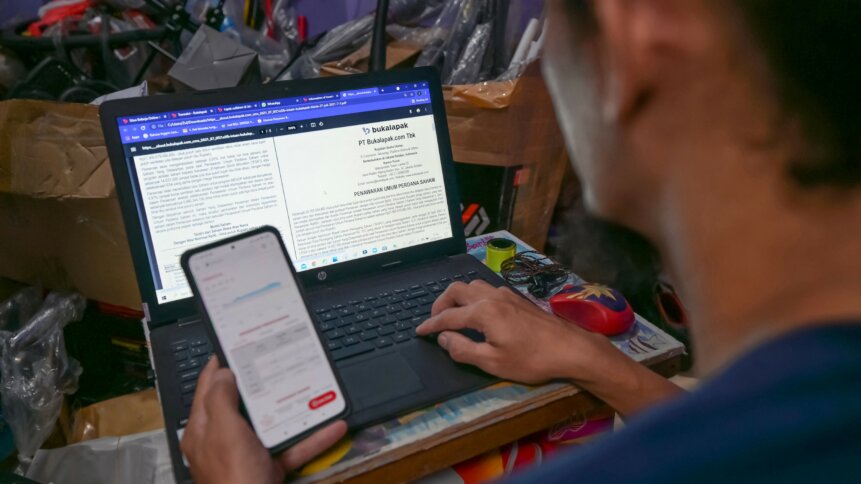
(Photo by Kenzo TRIBOUILLARD / AFP)
Why are cybercriminals continuing to target Google Chrome?
As more and more of the work is done in the browser, it becomes an essential, yet vulnerable, entry point that if compromised, could give cybercriminals access to the most sensitive organizational data. Google Chrome is by far the most popular browser, which maximizes the potential impact of each zero-day developed by the attacker.
Google has patched 15 Chrome zero-day vulnerabilities since the beginning of 2021, clearly indicating that Chrome has become one of the favorite targets of threat actors. Additionally, “patch fatigue” plays an important role in the race to patch vulnerabilities before they are exploited. Although Google regularly releases updates for Chrome, users who are constantly bombarded with updates aren’t updating their browsers fast enough, or not at all. This allows cybercriminals to exploit known vulnerabilities in popular software, even if patches are available.
YOU MIGHT LIKE

Best web browsers round-up for business use
How browsers can be exploited and the most common types of browser attacks?
Browsers can be exploited through their code that allows attackers to abuse flaws and vulnerabilities in both the browsers and their extensions or websites. When a browser that contains a flaw load into a malicious website, the attacker can take control of the browser and even the entire endpoint.
Once in the browser, attackers can cause serious damage by stealing credentials like passwords and access tokens, delivering ransomware attacks, and gaining access to sensitive data. Usually, browser attacks do one or more of three things:
- Exploit vulnerabilities in the browser itself
- Abuse legitimate browser functions such as password saving or activity monitoring
- Redirect users to malicious or phishing websites and trick the user into entering sensitive data
A few common types of browser attacks include zero-day browser exploits, browser extension attacks, and man-in-the-browser attacks.
Will browser attacks continue in 2022 and beyond?
Yes, it is likely that browser attacks will not be going anywhere as we enter 2022. Due to the growing reliance on SaaS, more and more core business processes are taking place in the browser, which makes it an attractive target. Now that hybrid working is the standard and the browser is the new endpoint, enterprises need to take action to protect against these risks.









