Cybercriminals manipulate IT burnout to launch disruptive attacks
Cybercriminals continue to find new methods to reshape the modern threat landscape. Despite organizations investing in more cyber protection technologies, cybercriminals always seem to have an upper hand and are still causing havoc to most businesses.
According to VMware’s Global Incident Response Threat Report, there has been a drastic rise in destructive attacks. Cybercriminals are now deploying advanced techniques to deliver a more targeted, sophisticated attack that distorts the digital reality, be it via compromising business communications or the manipulation of time.
The report analyzes how attackers manipulate reality to reshape the modern threat landscape. In the past, threat surfaces can be derived from both potential and identified cyberthreats affecting a particular sector or group. The evolving threat landscape today makes it harder to pinpoint exactly how, where and when cybercriminals may strike.
“Today, we’re seeing a nexus between nation-states and cybercriminals continue to rapidly advance the development of increasingly sophisticated and destructive cyberattacks, combined with the broadening of the attack surface as a result of COVID-19,” said Tom Kellermann, VMware’s head of cybersecurity strategy.
Tom pointed out that with the convergence of the digital and physical worlds, everything can be manipulated by modern-day attackers. For Tom, the reality is that first adopters of advanced technologies, such as artificial intelligence (AI) and machine learning, are often cybercriminals on the dark web and in nation-states’ intelligence communities.
Weaponizing new technologies
As with any new technology, before organizations adapt them to their security, cybercriminals are already working on ways to discover vulnerabilities or how the technology can be manipulated to serve them as well.
For example, AI in cybersecurity was initially claimed to revolutionize threat hunting and improve protection. However, cybercriminals have also found ways to tap AI to avoid detection by security software and infiltrate companies. IoT devices that are meant to help improve work productivity can also be easily weaponized by criminals, causing more problems to organizations. For example, an IoT device in a manufacturing plant can be tempered by cybercriminals to send wrong or delayed information.
While it may be hard to avoid the weaponization of new technologies, there are some tools to protect them. However, with more technologies and tools being implemented, the workload for IT teams is also getting heavier, which can make them error-prone at times. Cybercriminals know this and are now looking to leverage workplace burnout as well.

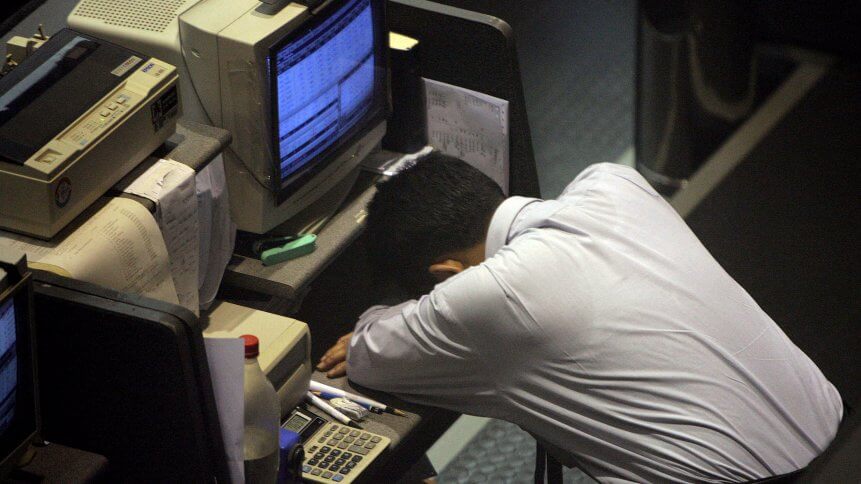
(Photo by Bryan R. Smith / AFP)
Dealing with burnout
In most organizations today, IT teams are finding it harder to counter complex attacks, especially in gaining visibility into new environments such as the cloud, containers, and business communication applications. In fact, about 51% of IT teams are struggling to cope with the level of attacks, due to mental health concerns and high job expectations, leading to burnout over the past year.
“Burnout is a huge issue with incident response teams, who are handling a spike in engagements in what is still a largely remote environment,” explained Rick McElroy, principal cybersecurity strategist at VMware.
YOU MIGHT LIKE

How can AI derail the organization’s cybersecurity?
“It only further underscores the need for leaders to build resilient teams, whether that means considering rotations of work, empowering individuals to take mental health days or any number of other initiatives aimed at nurturing personal growth and development,” McElroy added.
At the same time, targeted victims experience destructive attacks more than 50% of the time. Cybercriminals are achieving this through emerging techniques, like the manipulation of timestamps, or Chronos attacks.
Catalyzed by the shift to remote work, some also experience adversaries leveraging business communication platforms to move around a given environment and launch sophisticated attacks. With more businesses moving to the cloud, cybercriminals have also continued to exploit these environments as more than a third of attacks were targeted at cloud workloads.
As McElroy puts it, businesses need to build more resilient teams and empower their employees, especially those dealing with security in order to have a better work-life balance. Not only will it help them focus on dealing with threats but also reduce any chance of human errors.
After all, cybercriminals can experience burnout themselves, explaining why they operate in teams and leverage on various technologies when infiltrating companies. The same should also be practiced by organizations.









