
Business continuity is critical for organizations, disruptions to daily operations need to be avoided as much as possible. Many companies have invested in technologies to ensure their data is secured and have sufficient business continuity tools to run their workloads with minimal trouble. But have they similarly secured their supply chains?
Cybercriminals continue to find methods to wreak havoc on various industries globally. Be it large or small-medium enterprises (SMEs) ransomware attacks continue to find ways into companies and disrupt businesses. The supply chain is now being heavily targeted by cybercriminals as its the most important aspect for any business. So how can businesses continuity be ensured when the supply chain is disrupted?
One of Sweden’s largest grocery chains, Coop, was forced to close at least 800 stores over the weekend due to a cyberattack on a software provider in the US. The software provider, Kaseya, a managed services provider (MSP) manages Coop’s point-of-sale tills and self-service checkouts went offline, in an attack that also affected close to 200 other businesses as well.
According to a statement by Kaseya, its VSA product has been a victim of a sophisticated cyberattack but it only affected a very small number of their on-premises customers only. The statement also mentioned that Kaseya will bring back its SaaS data centers back on-line on a one-by-one basis starting with the EU, UK and APAC data centers followed by its North American data centers.
They are still working on their on-premises infrastructure and said that all on-premises VSA servers should continue to remain offline until further instructions from Kaseya about when it is safe to restore operations. Kaseya also warned customers who experienced ransomware and receive communication from the attackers should not click on any links as they may be weaponized.
The cyberattack on Kaseya highlights the increasing concern of who cybercriminals are now targeting organizations around the world. With ransomware still being the main threat, cybercriminals are now narrowing their target list and can be clearly seen to target industries that will have an adverse impact on the globalized supply chain.
Not the first time
Kaseya is just one of the many victims in recent months that have experienced global disruptions due to cyberattacks. Colonial Pipeline was the victim of a massive cyberattack that saw it shut down its fuel distribution network, sparking fears of fuel shortage while the world’s largest meat processor company JBS had its network hacked, temporarily shutting down some operations in Australia, Canada, and the US. The shutdown not only affected thousands of workers but also had a big impact on global meat supply.
Last year, GPS maker Garmin also experienced a ransomware attack which left thousands of its users frustrated as they were unable to access their data. These attacks were not only well-planned but also well-executed, as the cybercriminals knew the weak points to target.
The 2021 Unit 42 Ransomware Threat Report by Palo Alto Networks states that the average ransom paid for organizations increased from US$115,123 in 2019 to $312,493 in 2020, a 171% year-over-year increase. Additionally, the highest ransom paid by an organization doubled from 2019 to 2020, from US$5 million to US$10 million. In 2020, the highest ransomware demand grew to $30 million.
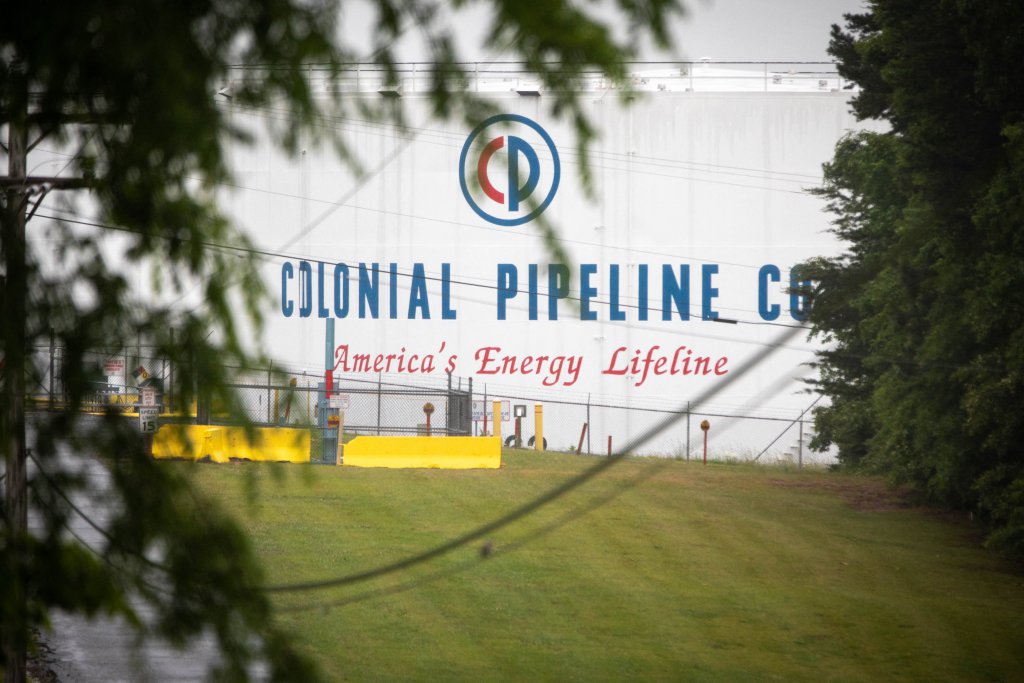
(FILES) A Colonial Pipeline storage site in Charlotte, North Carolina on May 12, 2021. (Photo by Logan Cyrus / AFP)
Cybercriminals are targeting MSPs
Interestingly, unlike Garmin, Colonial Pipeline and JBS, Kaseya is an MSP. So why are cybercriminals targeting an MSP instead of focusing on other businesses?
According to Kevin Reed, the CISO at global cyber protection company Acronis, MSPs are high-value targets as they have large attack surfaces, making them juicy targets to cybercriminals. A single MSP can manage IT for dozens to a hundred companies. So, instead of compromising 100 different companies, the criminals only need to hack one MSP to get access to them all.
Reed explained that MSPs can be compromised via a variety of techniques, with poorly configured remote access software among the top attack vectors. Cybercriminals use vulnerabilities, like the lack of 2FA, and phishing to get access to MSPs management tools and eventually to their clients’ machines.
“While we advise to never pay the ransom, the reality is businesses that can’t rely on their incident response plan still pay the criminals – as seen in recent JBS and Colonial Pipeline cases. Ransomware demands against the breached clients in this case varied from the initial demand of $44,999 to $5 million – with further possibility of steep fines from the authorities for those opting to pay,” he added.
Meanwhile, security researchers believe the attack may have been carried out by REvil, a Russian cybercriminal group. According to the FBI, the group was also involved in the hacking of meat processor company JBS back in May.
Business recovery
US President Joe Biden and Russian President Vladimir V.Putin met several weeks earlier in Geneva to address the growing concerns of cyberattacks. Biden gave Putin a list of 16 types of critical infrastructure that should be “off-limits” from cyberattacks, such as the energy and water sectors, and also pressed the Russian premier to stop harboring Russian cybercriminals and hold them accountable for attacks overseas.
At the same time, the European Union (EU) is set to have a new cybersecurity task force that will respond to attacks across the bloc. The ‘Joint Cyber Unit‘ would allow member states hit by cyberattacks to ask for help from other countries within the EU, including through rapid response teams that will be deployed to fight off hackers “in real-time”.
While it may be some time before the cybercriminals behind the recent ransomware attacks are brought to justice, businesses need to have a recovery plan on hand should they fall victims to such attacks. Reed suggested businesses review and re-evaluate their MSPs as a potential source of risk to their business. Unneeded access should be revoked and check with MSP for security measures in place should an attack happen.
More importantly, businesses need to have a proper backup and recovery plan in place should they fall victim to any cyberattack. Paying the ransom may be the way out for business continuity but there is no guarantee that cybercriminals will not strike the business again once the ransom is paid. The best option is to have a proper backup and recovery plan.
For the case of Coop, if they had a backup payment option for their stores, perhaps they could have switched to it. They would have been able to keep their stores open and not suffer any downtime losses. Businesses also need to make sure they have a copy of their data backup and stored securely, either offline or on a separate platform from their main services.
These options may cost a bit more but in the long run, backup and recovery is the best way to deal with ransomware without having to disrupt business operations and enabling business continuity.









