Ransomware attack shuts down major US oil pipeline
- A Russian criminal group may be responsible for a ransomware attack that shut down a major US fuel pipeline
- The operator, Colonial Pipeline, said it had halted systems for its 5,500 miles of the pipeline after the attack
- Unclear when the pipeline will resume operations
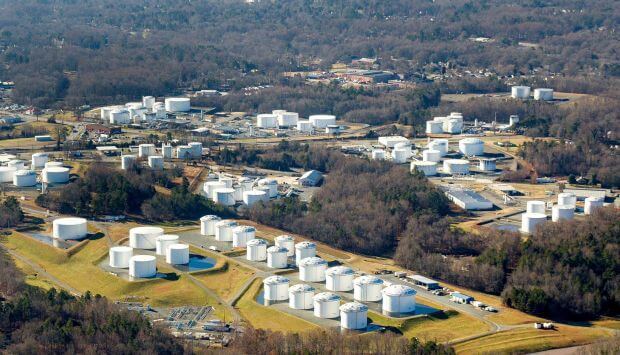
One of the US’ largest pipelines, which carries refined gasoline and jet fuel from Texas up the East Coast to New York, was forced to shut down after being hit by a ransomware attack. Sources are saying that a Russian criminal group may be responsible for it, vividly demonstrating the vulnerability of energy infrastructure to cyberattacks.
In a rather vaguely worded statement, the operator of the system, Colonial Pipeline, said that it had shut down its 5,500 miles of pipeline, which it says carries 45% of the East Coast’s fuel supplies, in an effort to contain the breach. Earlier that same day, there were disruptions along the pipeline, but it was not clear at the time whether that was a direct result of the attack, or of the company’s moves to put a halt to it.
“We proactively took certain systems offline to contain the threat, which has temporarily halted all pipeline operations, and affected some of our IT systems,” the company said in a statement. Colonial’s network supplies fuel from US refiners on the Gulf Coast to the eastern and southern U.S. and transports 2.5 million barrels a day of gasoline, diesel, jet fuel, and other products through 5,500 miles of pipelines, according to the company.
Bloomberg’s report indicated that the shutdown of the major oil artery linking the Gulf Coast in the middle east to East Coast markets may not spell Armageddon provided the situation is resolved quickly. “Disruption to energy markets should be as minimal as when shutdowns occurred in 2016,” it said.
Who’s responsible for the ransomware attack?
As the FBI, the Energy Department, and the White House delved into the details one day after the attack, Colonial Pipeline acknowledged that its corporate computer networks had been hit by a ransomware attack, in which criminal groups hold data hostage until the victim pays a ransom. The company said it had shut the pipeline itself, a precautionary act, apparently for fear that the hackers might have obtained information that would enable them to attack susceptible parts of the pipeline.
Preliminary results of the investigation at this point suggest the attack was the handiwork of a Russian criminal group DarkSide that operates in Eastern Europe, according to two officials briefed on the probe. Federal officials are continuing to firm up their findings and are actively trying to determine whether a foreign nation could either be behind the attack or work together with the criminals.
According to a top Reuters cybersecurity reporter, DarkSide has its own website on the dark web that features an array of leaked data from victims who it claims failed to pay the ransom. It claims that the group has made millions from cyber extortion. In fact, in recent months, officials note, the frequency and sophistication of ransomware attacks have soared, crippling victims as varied as the District of Columbia police department, hospitals treating coronavirus patients, and manufacturers, which frequently try to hide the attacks out of embarrassment that their systems were pierced.
Undeniably, attacks on critical infrastructure have been a major concern for a decade, but they have accelerated in recent months after two breaches — the SolarWinds intrusion by Russia’s main intelligence service, and another against some types of Microsoft-designed systems that has been attributed to Chinese hackers — underscored the vulnerability of the networks on which the government and corporations rely.