The retail giants at serious risk of cyber-attacks

- Websites belonging to retailers like IKEA and Walmart are massively expansive, easy to use, and personalized, but heightened UX can come at the cost of security
- These sites are incredibly complex, comprising thousands of web apps which combine to create a large attack surface
Online shopping surged 30% amid the global pandemic — and things are only going to ramp up further as we enter the holiday shopping season.
While all that extra traffic’s great news for large e-commerce players, the frenzy represents a huge opportunity for attacks, from credit card fraud, DDoS, credential stuffing, floods of fake spam reviews, even ransomware — as both retailers and their customers ease their guard.
In spite of increasingly advanced cybersecurity measures taken by retailers, disruptive cyber-attacks have become more common — according to Bloomberg, nearly 400 million customer records were exposed through attacks on retail companies in the last year.
Much of the risk comes down to retailers’ need to create user-friendly websites. User experience (UX), or creating visits that are enjoyable, personalized and quick and simple, is a top priority for driving repeated sales.
But that UX can come at the cost of thorough security measures which can seem time-consuming and difficult. And behind the seemingly simple interfaces of retail websites, housing hundreds of thousands of easily-navigable products and flexible services, are complex ecosystems of web applications to make it all work.
All these applications combine to amount to massive attack surfaces, and that means some of the world’s best-known online retailers are also some of the most difficult to defend.
Security professionals in the sector face a bigger challenge than ever to detect where their companies are most at risk, and how a potential breach could arise from within complex digital ecosystems.
Web application security
Web applications accounted for some 43% of data breaches in 2019, according to a report by Outpost24, which found — with a risk score of 35.1 out of 42.3 — that US retailers like Walmart, Costco, Amazon US, and Kroger have a significantly larger attack surface than European counterparts.
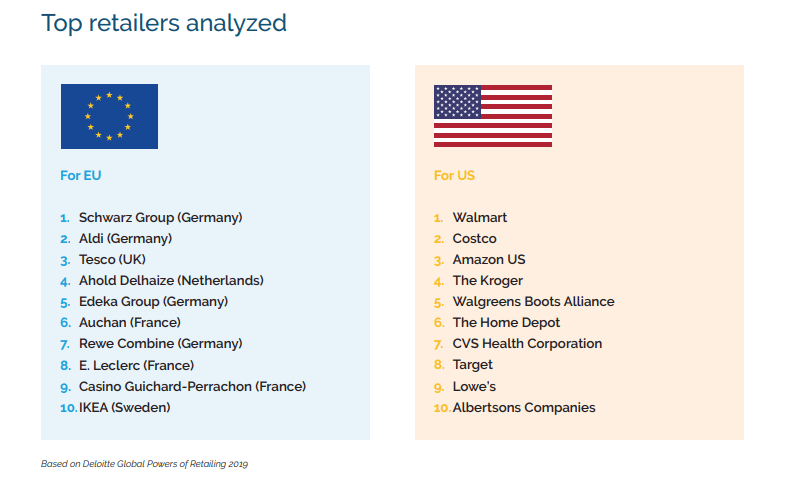
Top 10 retailers in both the US and EU included in the study. Souce: Outpost24
“This is a worrying trend, as we all know the larger the attack surface, the more likely it is for bad actors to find holes in security defenses and execute potential exploits,” read the report.
Web application security is a well-known issue faced by organizations worldwide due to the sheer volume of applications they own — the majority they don’t even know exist.
In the US, Outpost24 found 3,357 publicly-exposed web applications running over 401 domains among the top retailers, with 8% of them considered as suspect (often test environments that have been left online, intentionally or unintentionally, providing a potential backdoor for bad actors to access the production database) and 22% of them running on old components.
Retailers in Europe didn’t fare too well either, with 2,799 applications running over 509 domains, with 4% considered as suspect and 27% of them running on old components containing known vulnerabilities.
Overall, US companies did better than their transatlantic peers in new technology adoption — but that makes them twice as likely to be running shadow IT, which opens more doors for attacks.
“Hackers are masters of reconnaissance,” read the report, ready to go to great lengths to identify weak spots in their target by looking at how many pages there are per application. If there is outdated software in the architecture and what CMS and associated vulnerabilities it’s built on.
Outpost24 also examined the components that were used to develop the web applications and discovered that 90% of EU retailers and 50% of US retailers are currently running outdated jQuery versions on their applications which could expose them to common cross-site scripting attacks.
Furthermore, the top retailers are found to be using a variety of outdated servers to run their applications, making their shared hosting environments vulnerable to unauthorized access through potential exploitation of known vulnerabilities.
If not adequately managed, all these elements combine to present opportunities for attackers to gain footholds in systems and cause potentially catastrophic breaches.
“How the web application is built and developed is a key risk indicator if you know where to look,” said Stephane Konarkowski, Security Analyst at Outpost24.
“To avoid data breach and the loss of customer trust and revenue, retailers must address security hygiene as an essential step to protect their web applications and ensure the attack surface is kept at a minimum through continuous assessment.”









