5 steps to making IoT networks more secure
- The rise of IoT in business has brought increased levels of risk to security while presenting new and complex challenges for business leaders
- Protecting and securing ecosystems is a severe problem that needs to be addressed to leverage IoT successfully
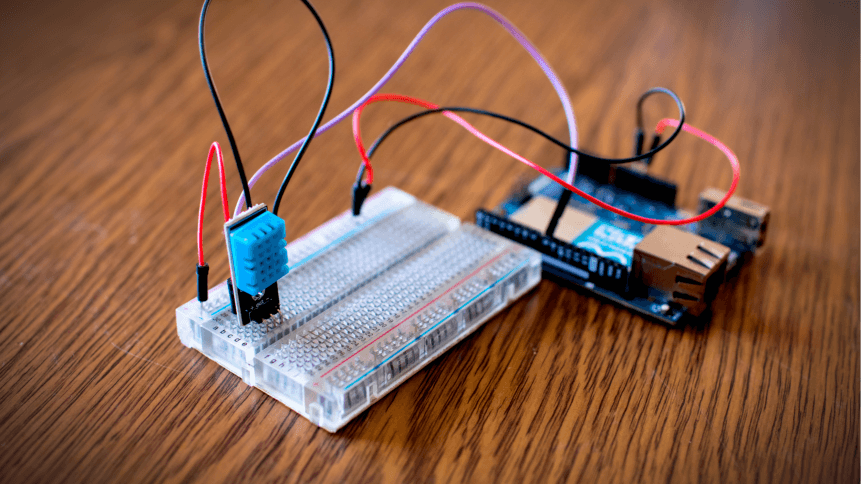
Internet of Things (IoT) is an undeniable buzzword referring to the exciting possibilities of a world connected by hardware and sensors. It’s a big, broad-sweeping concept and it continues to have a big security problem.
From automated security systems to laptops, IoT-enabled devices are growing at a rapid pace according to Gartner, with up to around 20.4 billion devices already said to be connected today. That number continues to grow larger, driven by ceaseless uptake in the business and consumer sphere, sophisticated sensors, more computing power in the cloud, and at the edge, and increasingly reliable mobile connectivity.
IoT use cases are vast– hardly any industry is exempt from its benefits. In the utility sector, for example, sensors in water pipes could feedback maintenance data to programs that predict when fractures are likely to occur. In precision agriculture, crop health can be revealed thanks to sensors that measure light, humidity, temperature, soil moisture, and feed it back to farmers.
Internet of Things technology is the backbone of the smart city concept, where sensors gather data on the behavior of citizens in order to optimize and improve public services, sustainability, and quality of life.
But in a world of ever-more sophisticated cyberthreats accelerated by the pandemic, the growing number of devices creates a greater attack surface for bad actors. Not only are there more (and new) opportunities for information to be compromised but more sensitive data is bring shared through IoT as the technology becomes more advanced and greater reliance is placed on it, making the risks of a breach exponentially greater.
“Take the smart home as an illustrative example. Imagine a garage door opener with the added functionality to deactivate the home alarm upon entry,” reads a report by Deloitte.
“This is a convenient feature for a homeowner entering their home in a hurry. However, now the entire alarm system could potentially be deactivated when only the garage door opener is compromised. The broad range of connectable home devices—TVs, home thermostats, door locks, home alarms, smart home hubs, garage door openers, to name a few — creates a myriad of connection points for hackers to gain entry into IoT ecosystems, access customer information, or even penetrate manufacturers’ back-end systems.”
If we escalate this same weak-link concept to an IoT-enabled traffic light system or a smart factory, it’s easy to imagine the level of destruction that could be inflicted by a single compromised device or vulnerable system.
As more businesses embrace the advantages of IoT and more than half of IT professionals recognize IoT security as a top priority, here are five basic steps that can be taken to ensure IoT networks are secured.
End-to-end encryption: The best way to secure connected devices is to ensure that data is encrypted at every intersection. End-to-end encryption protects information that travels from point to point while preventing cybercriminals from intercepting any sensitive data.
Install device and software updates: Be sure when purchasing a device that the vendor provides updates and applies them immediately. Alternatively, automatic updates should always be implemented to ensure they are installed on time.
Choose the right cybersecurity provider: Leveraging IoT successfully requires a reputable cybersecurity and antivirus provider. It’s vital to choose protective solutions that are uniquely accessible and that have a proven track record in preventing cyberattacks.
Secure mobile devices: At the end of every business day, it is vital to ensure that connected devices like tablets and mobiles are checked in and locked up. Any device with important information that goes missing could be compromised, so it is essential to also ensure passwords are strong.
Disable unused features: To reduce the potential for cyber attack opportunities, it is critical to always check available features while disabling any that you don’t intend to use.










