Quantum computing as a weapon? The looming cryptographic cyber-threat

- Quantum computing will bring revolutionary benefits to businesses, but in the wrong hands, it could present itself as a powerful ‘weapon’
2020 has been a tough year, and a spike in opportunistic cybercrime has only been a ‘jewel’ in its crown. The work from the home revolution which took place overnight highlighted to us just how unprepared we were to keep a distributed workforce protected. Cybercriminals were lightning fast to emerge and capitalize on the crisis and confusion.
Cybersecurity is a complex beast. Despite the inch-thick, Teflon-coated plate we place around the IT network, it only takes one hasty click of a rogue phishing link to open a backdoor for cybercriminals to take control.
While malware may become more sophisticated and the methods of attackers harder to detect, at present we are playing against a familiar if unrelenting foe. But the age of quantum computing will bring a force of adversity of new proportions.
“You might think that 2020 has been a rough year for cybersecurity, but we’re only just scratching the surface of what could go wrong,” Dr Ali El Kaafarani, founder of PQShield and research fellow at the University of Oxford’s Mathematical Institute, cheerily told us.
“Add quantum computers into the mix, and the entire foundation of today’s information security will be under threat.”
Hard to fathom though it is today, few disagree that quantum computing will be a revolutionary technology.
Heading towards a market worth of US$5.8 billion by 2025, every few months we hear of another milestone made by the likes of IBM or Google, bringing us closer to an age of quantum potential.
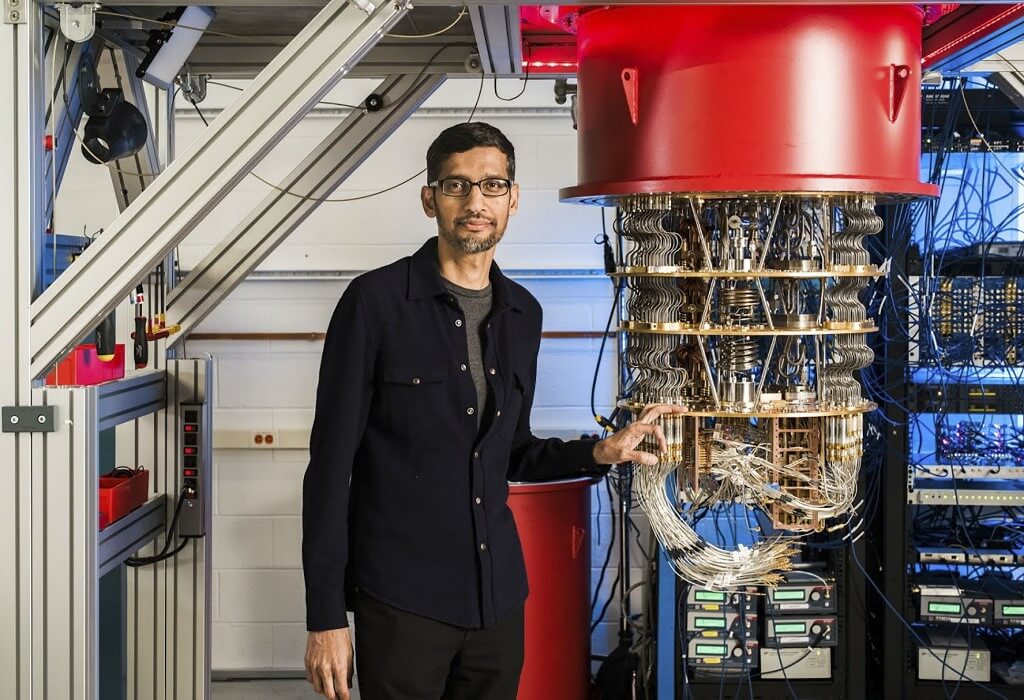
Sundar Pichai, CEO of Alphabet with one of Google’s quantum computers. Source: AFP
The quantum era
“Quantum computing is the future industry and infrastructure disruptor for organizations looking to use large amounts of data, artificial intelligence, and machine learning to accelerate real-time business intelligence and innovate product development,” according to Heather Wells, the IDC’s senior research analyst of Infrastructure Systems, Platforms, and Technology.
Theoretical use cases of the technology span anything concerning large, uncertain systems that need to be simulated, from predicting the financial markets to producing better, cheaper drugs.
But as the quantum dawn approaches, conventions challenged include our notions of how we can protect our machines and networks — which, as we know, are regularly proven to be far from airtight. Of particular concern is quantum computing’s potential to eventually break encryption methods, which are used in varying degrees to safeguard data from individual to state level.
“The scale of the quantum threat cannot be underestimated,” said Kaafarani. They will have the ability to smash through traditional public-key encryption, threatening the security of all sensitive information, past and present.
“Data across cars, planes, medical devices, servers, and countless other devices cannot be secured retrospectively; they must be protected now.”
A severe threat
The threat is too severe to ignore, but it’s not being overlooked. In fact, the US National Security Agency warned in 2015 it must ‘act now’ to safeguard its systems from the quantum threat, and The National Institute of Standards and Technology (NIST) initiated a process to define new, quantum-ready cryptographic standards.
That process is now in the final stages, and PQShield is a leading contributor to the project, with two out of the seven finalist algorithms having been co-authored and led by Kaafarani’s team.
The quantum computing cybersecurity threat comes down to the ease of which the technology will likely be able to break through existing methods of encryption. Existing types of encryption revolve around mathematical problems, such as integer factorization and discrete logarithm, which are difficult for classic machines to solve because of their computational limitations. But once quantum computers arrive, they will be able to easily solve those mathematical problems and thus break the most common form of modern encryption — public-key cryptography.
“Our team is designing new post-quantum cryptographic solutions for software, hardware, and communications, which go way beyond those encryption methods, using different mathematical fields and principles that offer the complexity necessary to stump even a quantum computer,” said Kaafarani.
He added confidence that there are no algorithms that can solve the type of mathematical problems that PQShield is using to build the next generation of public-key cryptography.
Raising alarm bells
Quantum computing advances have been incremental to date, but Kaafarani believes there have been notable advances in the last few years that have raise alarm bells for those looking at the application of the technology “as a weapon”.
In late 2019, we started to see back and forth between Google and IBM about achieving ‘quantum supremacy’ when it came to performing certain calculations and then we saw the world’s first real-world application of the technology outside of these calculations by Volkswagen in 2019.
“At this current pace of innovation, it’s not unfeasible that we could see a nation-state or well-capitalized company develop a rudimentary quantum computer within the next decade. We might not know about it, it would be a huge competitive advantage and they might choose to keep it secret,” Kaafarani said.
“While different industries have different timelines depending on how long their product life cycles are, it’s fair to say that for data across cars, planes, military vehicles, power stations, satellites, IoT – anything that will last over 10 years — this threat needs to be considered right now.”
While with current computers, we lack the practical means to do so due to computational and memory limitations to do so, a malicious actor using a quantum computer could gain access to the secret key corresponding to any public key.
An attacker could use that access to forge the signature of a software update and push an update to, say, an engine part and it will not know it’s forged, Kaafarani explained: “This would then enable the bad actor to alter the operations of an aircraft through that part as they wish in secret. That’s also what makes the famous ‘harvest now decrypt later’ attack possible.”
It is then vital to act now to ensure a smooth yet secure transition into the powerful quantum era.