Garmin ransomware – a targeted, ‘destructive’ strain of WastedLocker

- Multinational tech firm Garmin was victim to a ransomware cyberattack, causing outages to key services
- The ransomware is now confirmed to be WastedLocker
- Files obtained by Bleeping Computer indicate that Garmin acquired a decryptor, suggesting a payment was made to attackers
Garmin’s long-running outage last week was called by commentators as ‘case study’ in how not to handle an IT failure. But now it could draw ire for its response to a threat dogging every large business today: ransomware.
The multinational GPS and fitness tech company – valued at more than US$18 billion – suffered a worldwide outage on July 23, which prevented users from uploading data from their devices to Garmin connect. The outage also affected its navigation service for the aviation sector, FlyGarmin.
The impact of the outage was such that fitness app Strava – onto which Garmin users can upload their activities – saw activity uploads drop dramatically.
Garmin remained quiet on the outage to begin with, presumably as it weighed up its public response. Many in the cybersecurity industry, however, were quick to guess the cause – some even correctly identifying the organization likely behind it as the Russian, state-backed hacker group Evil Corp, and the ransomware behind it, WastedLocker.
Garmin later confirmed it had been the “victim of a cyberattack that encrypted some of [its] systems.” With hackers reportedly demanding a fee of US$10 million, the outage continued for four days in total, before services began to be restored.
According to files reviewed by Bleeping Computer, Garmin obtained the WastedLocker decryptor from July 24 to July 25, indicating that a transaction took place between the ransomware victim, or a mediator, and the attackers.
Bleeping Computer reports that it gained access to an executable created by the Garmin IT department to decrypt a workstation and then install security software. There is no known weakness for WastedLocker, meaning that decryptors cannot be made for free. The publication even successfully verified the decryptor, using it to unlock a virtual machine encrypted with a WastedLocker sample.
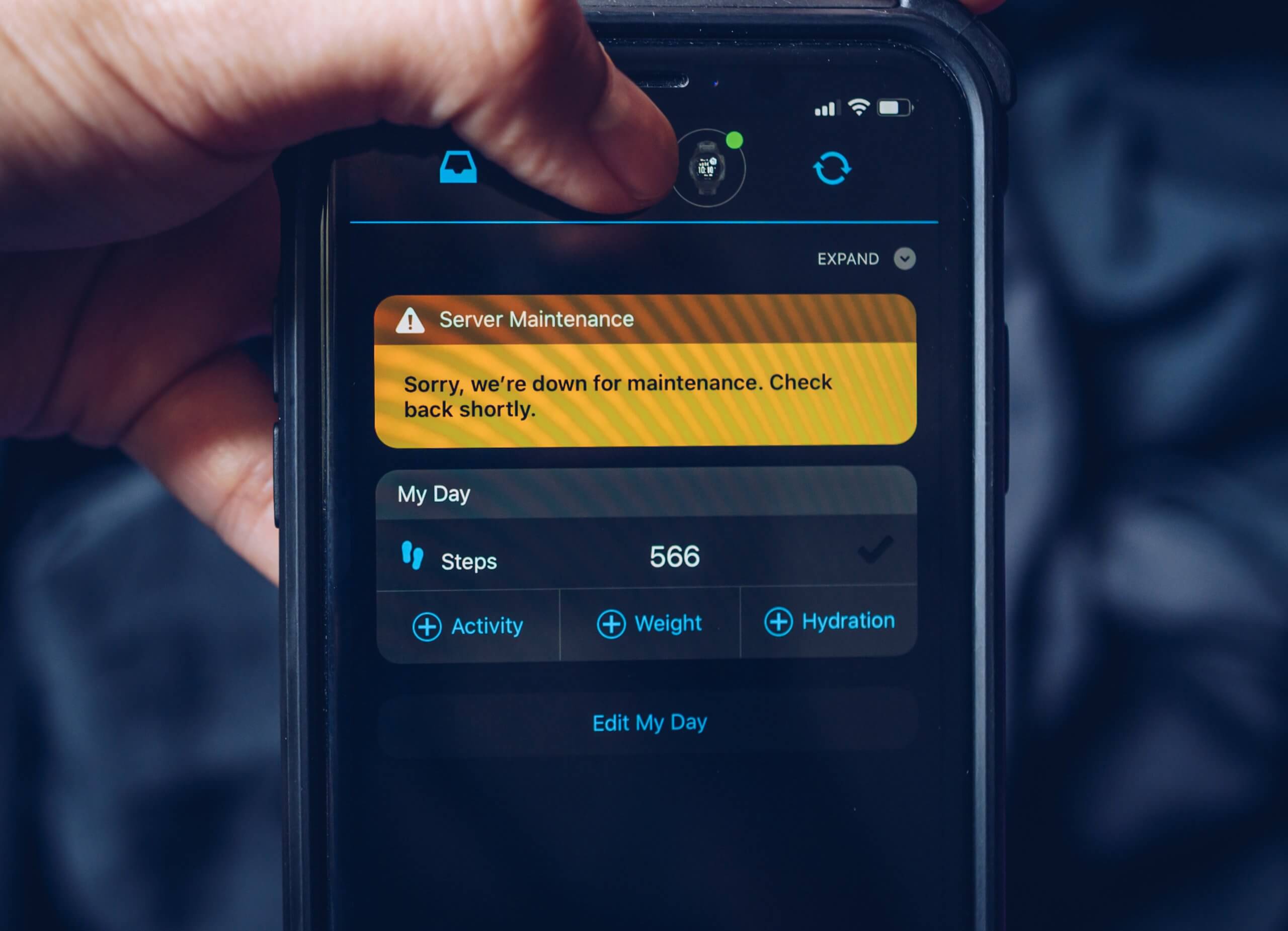
The notice in Garmin app showing on smartphone screen about incident and service interruption caused by ransomware attack. Source: Shutterstock
The decryptor obtained included references to cybersecurity firm Emsisoft and Coveware, a ransomware negotiation service. Asked for comment, Coveware said it didn’t discuss ransomware attacks reported in the media, while a representative from Emsisoft said they couldn’t comment on specific cases: “[…] generally speaking, Emsisoft has no involvement whatsoever in negotiating or transacting ransom payments. We simply create decryption tools,” said Emsisoft threat analyst, Brett Callow.
Evil Corp is on a US sanctions list, meaning any dealings with it – even via a third party – could lead to fines from the government. Those sanctions also meant that Coveware had allegedly placed WastedLocker on a restricted list ahead of the attack in early July.
According to Kaspersky, the ransomware has become noticeably more active since the first half of this year, but this particular version was designed to specifically target Garmin, and contains several unusual technical aspects.
The first is its User Access Control (UAC) bypass technique. Once launched on a compromised device, the Trojan checks whether it has high enough privileges. If not, it will attempt to silently elevate its privileges by tricking a legitimate system binary into launching the Trojan’s body hidden in an alternate NTFS stream.
In addition, the sample of WastedLocker analyzed from the Garmin attack used a single public RSA key — the type of key used to encrypt the files.
This would be somewhat of a weakness if the malware were to be distributed far and wide. The decryptor would only have to contain the one private RSA key to decrypt everyone’s files. However, if the campaign is targeted — as it clearly was in this case — a single RSA key is an effective approach.
“This incident only highlights that there is a growing trend of targeted crypto-ransomware attacks against large corporations — in contrast to the more widespread and popular ransomware campaigns of the past, like WannaCry and NotPetya,” said Fedor Sinitsyn, security expert at Kaspersky.
“While there are fewer victims, these targeted attacks are typically more sophisticated and destructive. And there is no evidence to suggest that they will decline in the near future. Therefore, it’s critical that organizations stay on alert and take steps to protect themselves.”
Key to ransomware’s continued danger is its success – a study by IBM Security’s X-Force found that 20% of compromised organizations have paid ransoms of more than US$40,000. But the figure is likely much higher, since not many companies would choose to go on the record. There have even been reported instances of ‘highly-specialized’ companies claiming to be able to ‘break’ systems from ransomware, but simply taking their clients money and paying off the attackers themselves.
Emsisoft’s Fabian Wosar spoke to TechHQ ahead of the attack on Garmin, and emphasized his regret at ransomware victims choosing to pay the ransom when there are alternative solutions available: “I always find it kind of disheartening when we deal with ransomware victims who contact us after they’ve paid the ransom.
“And it turns out that they didn’t have to pay the ransom in the first place,” the ransomware expert said. Companies hit with ransomware will fare better with “a little bit of research.” Or just even “reaching out to a company like us would go a very, very long way.”
In the case of the so-far-unbreakable WastedLocker, however, paying the ransom may have been Garmin’s only choice.










