Legit Zoom downloaders could be packed with crypto-mining malware

Recording 200 million users per day in March – 20 times its figures for December – there’s a good chance that if you’re videoconferencing this week, you’ll be using Zoom.
The videoconferencing software has attracted some pretty severe scrutiny regarding its privacy settings – its makers have been accused of concealing truth around the capacities of the app’s encryption software, which made conversations and data vulnerable to hackers – and that controversy is making an opening for rivals and new contenders to challenge its market share.
Despite this pressure, though, it retains the top spot, getting thousands more downloads and installs by the day. It’s a hive of activity that has attracted the attention of opportunistic cybercriminals, who are packaging malware into legitimate Zoom installers in order to infect their devices with malicious programs.
COVID-19 scammers strike
The trend is just one of the latest ways opportunistic cybercriminals are targeting the frenzy and disruption caused by the coronavirus, as workforces try to quickly adapt to the changing circumstances while, of course, being concerned and distracted by the greater impact that COVID-19 is having.
There have been plenty of reports of phishing attempts disguised as updates regarding the spread of the virus, while more sophisticated scams are even seeing attackers pose as government or health officials to lure victims into surrending private and sensitive data.
With social distancing, and retail and services closures making e-commerce and streaming services even more popular, meanwhile, there’s ample opportunity for phishing attempts posing as a shipping order confirmation or even an expired Netflix account.
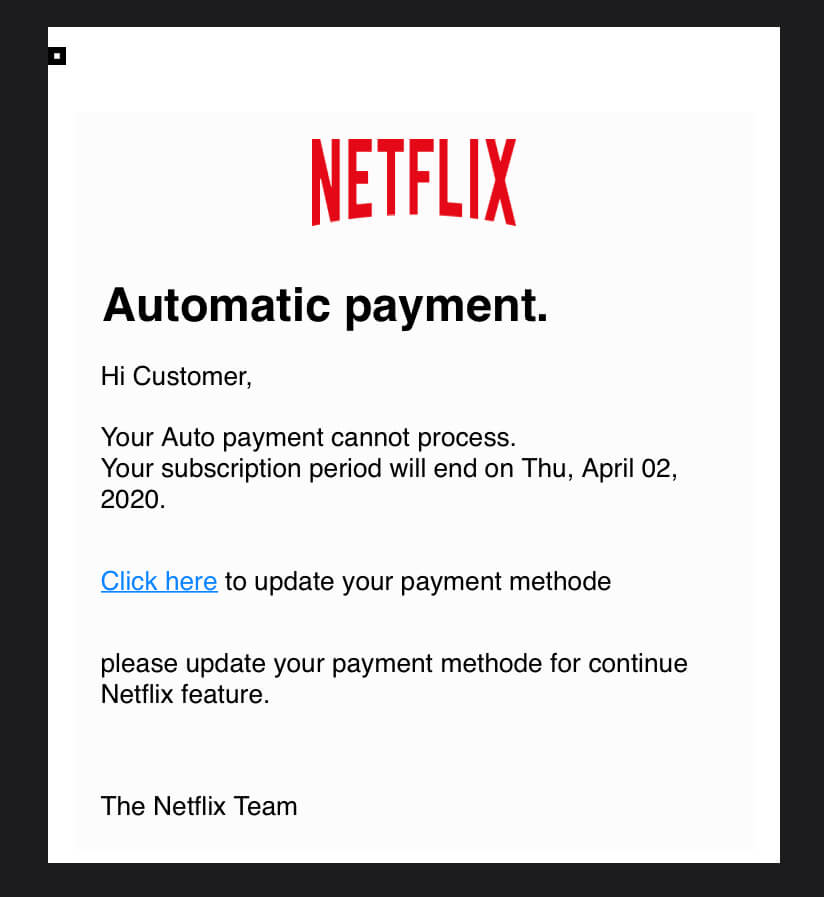
A (poorly) executed Netflix subscription phishing scam. Source: Author
The actors exploiting the sudden flurry of Zoom downloads have been reported to be attempting to conceal cryptocurrency-mining malware inside installers.
The malignant technique was flagged by Trend Micro researchers; “The compromised files are not from Zoom’s official download center, and are assumed to come from fraudulent websites.”
According to the report, the malware is hidden within legitimate Zoom downloads that launch a functional version of Zoom so the user is completely unaware. The trojan horse places a coin miner on the machine which harvests details about the computer, such as its CPU, operating system, video controllers, and processors — all useful information for mining activities.
It also intelligently checks whether antivirus systems are enabled and the coin miner will avoid running or exhibiting too much activity that may flash alerts or notify users.
Once a crypto miner is planted on a compromised host, bad actors will use the processing power of the infected computer to help mine for cryptocurrency. With activities shielded in the background, the attacks are carried out in series and could go on for months to avoid detection.
With that in mind, hackers of this category tend to target a large number of computers to profit from the cumulative cryptocurrency mined, so a spike in downloads for any software is an effective means to distributing the malware far and wide, to as many users as possible.
The need for endpoint security
While Zoom is the tool in question here, the report should be taken as a reminder to exercise caution and some measure when downloading new tools for collaboration and remote working, only using trusted and verifiable sources. IT heads must also look to invest in endpoint security solutions that can ensure their newly-distributed workforce is as best protected as possible.
“It seems the enterprise, and the millions of workers that have been rushed home to work remotely in the face of this pandemic, are still coming to terms with the new cyber threats that face them. And adversaries know it. Not only is there uncertainty about how to defend against it, but who is responsible for doing so,” Marco Essomba, founder of BlockAPT told TechHQ.
“Therefore, everyone needs to take on some responsibility. Organisations should implement an extra layer of protection by running an endpoint detection software across all devices.
“This will provide protection against unauthorized malware and other types of malicious programs from executing on employee devices. From the perspective of the individual user, keeping your Zoom software updated with the latest version and patches mitigates against most of these threats.”









