Will quantum computing make current cybersecurity practices obsolete?
We are lucky enough to be spectators in one of the most exciting technological races in the, albeit comparatively brief, history of computing.
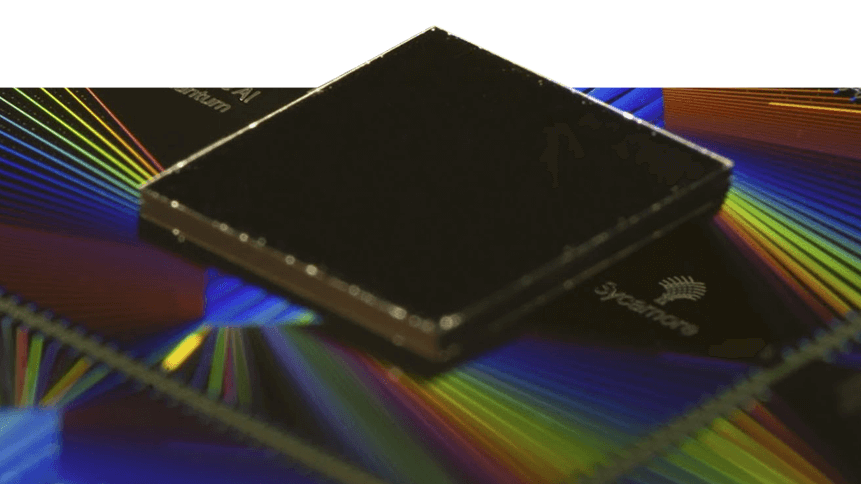
A matter of months ago, Google claimed a landmark breakthrough— its Sycamore quantum processor achieved ‘quantum supremacy’, solving a mathematical problem in 200 seconds that would have taken a matter of millennia for the world’s best supercomputer.
Google’s arch-rival in quantum, IBM disputed the claim, arguing that the same task could be undertaken by a conventional system in 2.5 days, with higher fidelity.
Either way, progress is being made at a rapid pace in the labs of these two tech giants. But, like any good competition, the outcome of which will triumph first is uncertain, if it is either of these two leaders at all.
“In the twentieth century, despite coming a full eight years after the Soviets’ initial space flight, America’s landing on the moon came to define the Space Race,” Shimrit Tzur-David, CTO and Co-Founder of Secret Double Octopus told TechHQ.
“For all we know, IBM may end up achieving the most definable moment in the twenty-first-century race for quantum supremacy. Only time will tell.”
For now, while R&D continues to thunder on, and interest from new entrants and prospective customers leads to forecasts that the quantum computing market may reach a worth of US$5.8 billion by 2025, we can only gaze at the possibilities for industry ahead.
While the ‘bit’ in a classical computer can have a value of either 1 or 0, the quantum bit (qubit), can be both at the same time. This enables multiple calculations to be performed at the same time.
Quantum computers will, therefore, work in concert with conventional systems, enabling businesses to enter a new universe of prediction modeling. That could open up untapped potential in the synthesis of new drugs and energy-efficient materials, as well as financial modeling, with other big data applications in aerospace & defense, BFSI, healthcare & life sciences, and energy & utilities.
Meanwhile, able to compute massive amounts of data, one of quantum computing’s central applications could be in artificial intelligence (AI), where it will be able to rapidly speed up the AI learning curve.
“Quantum computing will have a colossal effect on how businesses solve problems and will create entirely new markets as decision-making problems without linear solutions become solvable in reasonable amounts of time,” said Tzur-David.
“Solutions to NP [nondeterministic polynomial time] problems, which would otherwise necessitate ‘guess and check’ on an unimaginable scale, will be within reach.”
Tzur-David explained how one possible use case for quantum computing could be in calculating the optimal placement of charging stations for electric cars.
“Where do we put them? Creating the grid means congregating them around population centers while also preventing long stretches of road unequipped, so as to ensure that drivers do not get stranded. The possible combinations are endless.
“The statistical algorithms we currently use for this are merely a form of best guessing. Quantum computing could make these determinations more quickly and more accurate, enabling both businesses and governments to concentrate their efforts on other challenges,” he said.
The encryption cracker
As the dawn of quantum computing approaches, bringing with it vast new possibilities, conventions will be challenged, and that includes our notions of how we can protect our machines and networks— which, of course, are regularly proven to be far from airtight.
Of particular concern is quantum computing’s potential to eventually break encryption methods, which are used in varying degrees to safeguard data from individual to state level.
YOU MIGHT LIKE
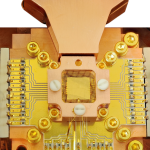
Accessible quantum computing is just around the corner
While quantum computers are not ‘there’ yet— it would take the power of 4,000 qubits to break today’s ‘strong’ encryption keys (Google and IBM are using 53-qubit processors)— the threat could be real in a matter of a few years, while weaker encryption algorithms will be vulnerable sooner.
“[…] quantum computers will render certain security solutions obsolete, such as RSA’s solution, which is based on finding prime multipliers of a large number, aka an asymmetric key,” Tzur-David said.
“Older asymmetric keys, which are shorter than today’s keys, will be especially vulnerable. But it doesn’t stop there. In PKI-based encryption, asymmetric protocols are used to share a symmetric key.
“Until now, whereas a 256-bit asymmetric key has been vulnerable, 256 bits for a symmetric key has been enough. In the face of quantum computing, it might not be enough.”
Of course, while clarity around threats is about as certain as the technology’s potential applications, the cybersecurity industry is wise to these developments, particularly in the face of the forthcoming development of cloud-based quantum-computing-as-a-service, which could put the computing’s power within the grasp of unfavorables.
“[…] agencies and institutions around the world are amassing data, readying themselves for the moment when quantum computing opens the door to a massive encryption break, one that is no longer theoretical.
“This threat against both asymmetric and symmetric keys has garnered the attention of enterprises, especially those in data protection.”
The new vulnerabilities presented by quantum computing power would “fundamentally change the idea of ‘due diligence’,” by the systems we currently trust to handle our data, said Tzur-David.
While reminding the public that credit card data was encrypted may have helped Marriott assuage some of the initial concern following its 2018 data breach— despite the key being stored on the same server— the same comment wouldn’t instill much confidence in the age of accessible quantum computers.
“If previously safe keys become unreliable, businesses will not be able to merely highlight whatever encryption they used. If their keys are old and short enough, all of their encryption could become meaningless,” Tzur-David said.
Make no mistake, while we have yet to truly enter an era where quantum computers form part of a new threat landscape, the existing technology— if it were “outside of Google’s lab today”— is already enough to break shorter encryption keys, which will be in use in servers, which will be housing sensitive data.
“The scary part is that it’s a matter of time. Once someone has amassed data encrypted with short keys, there’s no way to retrieve it. It’s just a matter of waiting until they can break it, and then game over.”
Tzur-David concluded: “For us to keep pace, we need to transition away from computational power as the be-all-end-all of cybersecurity. Multiparty computation, secret sharing, and other algorithms that serve information-theoretic security can provide new foundations.
“These solutions may be able to bypass quantum computing’s formidable power because their effectiveness is not measured in terms of power.”