Protect the smartphones in your business— we review secure comms technologies

When a new technology grabs the public imagination, predictions as to its short-term effects tend to be wildly off the mark, and it’s only when a technology becomes ubiquitous that the overall effects can be seen. Although the first cars began to appear at the end of the 19th century, it was the Model T Ford (111 years old this year), and the mass production of the motor car that began to literally change the planet.
Somewhat more recently, it was the launch of the Apple iPhone 3G along with baked-in support for a new concept — the Apple App Store — that shifted the world’s consciousness with regards to the phone. The first “house brick” phones were useful devices, but were only phones, and while the original iPhone was an attractive object, it was apps that have transitioned the smartphone to its current position as an integral part of most people’s lives.
Thanks to the smartphone and the apps that run on it, data is rapidly becoming the world’s most valuable commodity. Information interchange and communication are often, by default, digital, with the result that many businesses are now built entirely on data: several of the most prominent names in the data business world are more powerful and certainly better-resourced than entire countries. Data’s value is something that we, as a society, and the companies and organizations in which we work, are only just beginning to realize.
The emerging situation has not escaped the notice of criminal elements, nor sovereign governments all around the world. Hackers and various bad actors of every creed and color are more aware than most of data’s value, and can obtain, broker, and use information to their advantage. Usually, that usage is to sell the data, or ransom for its release (or variations thereon), but there is significant evidence of some government-led (or at least, governmental-sanctioned) use of illegally obtained data to influence world events at the most significant levels.

Source: Shutterstock
Educate or prevent?
What we as data-aware individuals must realize is that we are very much in the early days of a revolution. It’s only 11 years since the iPhone 3G’s emergence, so therefore protecting oneself online is not something we do automatically. When crossing a road, we look both ways, but ingraining that behavior has taken 111 years of traffic. When we pick up our phones, we’re starting a series of interactions, and naively, we’re not yet “looking both ways.”
Educating every user of technology is something that needs to be done, therefore, but there are massive pressures ranged against any efforts to do so. New services, new apps, and the latest tech all bring new opportunities, so the tendency is often to adopt or at least test the water. Getting over the idea of privacy, of not sharing, of withholding even seemingly innocuous information; this all flies in the face of new possibilities offered to us all daily, via every medium possible. And in the last 11 years, those messages center around the smartphone we all carry.
Protecting smartphones and their users is seemingly contrary to what the devices were intended to do. Sure, phones are all about effective communication, but both major phone operating systems (iOS and Android) are created by companies whose business comprises significantly of data. Therefore, these devices are not designed to be privacy-focused — arguably, quite the opposite.
Several companies, therefore, have emerged with solutions to issues of data privacy and cybersecurity on smartphones. After all, these are powerful computing devices being carried into workplaces across the globe, every day. Managing employees’ BYOD devices now gets (or should get) as much attention as protecting any endpoint in the organization, from the lowliest desktop to the production server. MDM (mobile device management) solutions push updates, security patches, monitor applications, and attempt to hit what is a series of literally moving targets.
However, most of these products are adjuncts or add-ons. Apps that sit on top of inherently insecure software will always be prone to attack or data exfiltration, be that by capturing voice data traffic, man-in-the-middle type data theft, or good old-fashioned device theft. The numbers of organizations wishing to ensure data security for their employees and management personnel properly are snowballing, and as devices “protected” by these peripheral offerings continue to be exploited, many organizations are turning to more reliable systems of data protection for smartphones.
Here at TechHQ, we’re focusing on two vendors of smartphone communication security provision, each with a different take on how organizations and businesses can better protect their intellectual property, their employees, and the data of their clients. It’s taken 11 years for these types of solutions to move from shady obscurity into the mainstream, but in this age of data being the most valuable commodity, protecting mobile comms in all its forms is surely a mainstream issue.
It’s worth noting that neither supplier featured here would claim that users can forego any further data protection training or lessons in basic data hygiene. But, until everyone with a smartphone begins to “look both ways” in a virtual world, significant tightening of smartphones security is undoubtedly a good thing.
Finnish company Bittium’s product line includes equipment and solutions for secure and tactical communications, among others, and its newest Tough Mobile 2 uses security technologies integrated in hardware and source code. Combined with the Bittium Secure Suite’s full set of services for secure communications (including an MDM), Bittium’s solutions offer companies the type of hardened communications systems that are practically unbreakable in any conceivable manner.

Source: Bittium
While the highest standards of protection (NCSA approved, for instance) might have seemed like overkill even five years ago, the numbers of high-profile data thefts are multiplying, and the results often go much further than a dent in a company’s PR profile. Because human error or fallibility is often at the root of data-related incidents, the Tough Mobile 2 provides for just about any occurrence. For instance, the software allows a separation (into multiple, switchable workspaces) of the phone’s operation, according to use-case. Hardened software combines with encrypted communications, bespoke, tamper-proof hardware, and a secure management portal to log and oversee the whole. Bittium has every base covered for the ultimate in smartphone security.
If your company or organization values its data and has personnel that need the very safest of mobile platforms possible, we suggest you read more here on the pages of TechHQ.
The Switzerland-based Silent Circle has chosen a particular use-case for its product: secure, encrypted communication between users. That means an app that provides voice to voice conversations encrypted end-to-end, also applied to text messages and file exchanges between users (up to 100MB file size per push or pull). Licensing for the high-end encryption service is on a per-user basis, paid monthly, and this provides too optional access to SCircle, a private network for Silent Circle users. All comms via SCircle are protected, and companies especially concerned with privacy can install their own hosted solution to provide the comms network, called Circle-in-Circle.
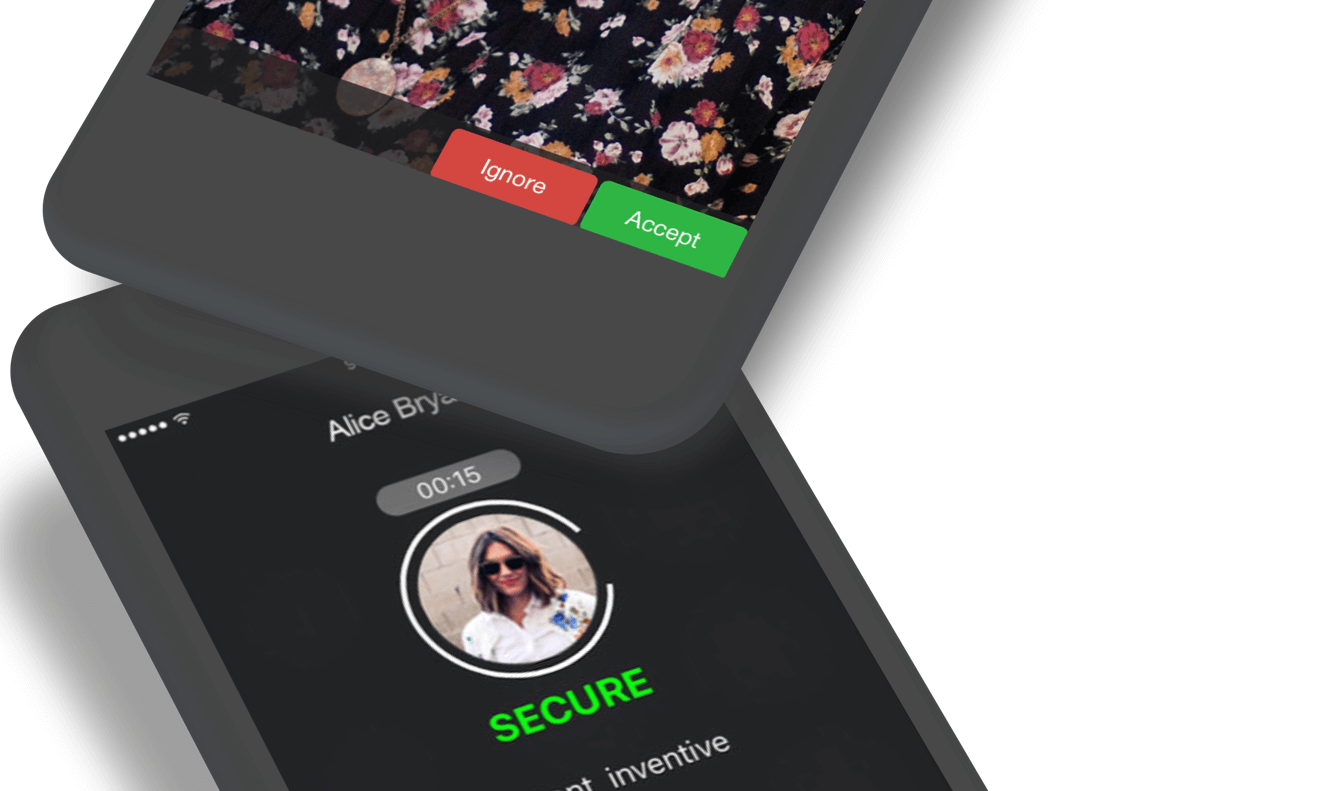
Source: Silent Circle
Built into the app is a host of business-oriented features, like group conference calls, video calling, and text messaging as well as direct user-to-user voice communications. Users can begin a call by speaking an optional short code to one another to ensure that the link is indeed safe, and any user can message another user with a “burn time” for the text or file. That means messages can be sent with an established deletion schedule so that even if a user’s device is compromised, there’s no trace of sensitive information.
The entire Silent Circle GUI uses the kind of user interface that every user will be familiar with, so for a few dollars a month, every person in your organization can be sure that all comms via the Silent Circle app is protected. Read more on the Silent Circle site, here.
*Some of the companies featured are commercial partners of TechHQ








