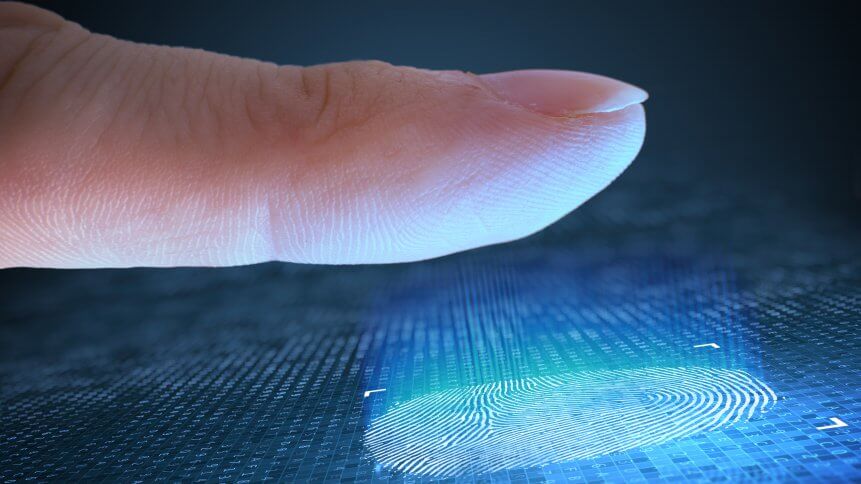
Biometric security protection shows its flaws
When an organization pays a commercial company to help protect itself, its customers and its employees, it’s expected that the contracted party does a half-decent job. That’s especially true in the world of cybersecurity protection, and even more relevant when the organization paying the bills is a defense contractor, a police force in a world capital, or a bank.
Unfortunately, the handing over of cash to help ensure security does not necessarily guarantee excellent results.
That’s the unfortunate truth being woken up to by the UK’s Metropolitan police force, numerous banks around the world and a pharmaceutical supplier— among many thousands of others. All had entrusted highly-sensitive details with South Korean outfit Suprema, which operates a web-based biometric security protection that provides access credentials to access secure premises.
According to a report in The Guardian and later confirmed by a post on the vpnMentor website, a database containing unhashed (unencrypted) biometric data was found in a publicly-available, unprotected database — that’s pictures of faces and fingerprints used to allow access. In addition to the biometric data, personal details, administrator usernames & passwords, facility access logs, security clearance level descriptions and lists were also exposed in handy, unencrypted plain text format.
Cybersecurity engineers’ coup
Israeli security researchers Noam Rotem and Ran Locar came across the unprotected database instance using automated scanning applications. Hackers deploy these types of routines too: the software scans IP blocks 24/7 and alerts users when a potential target is located.
YOU MIGHT LIKE

Has your business considered biometric security?
vpnMentor, the two researchers’ employer contacted Suprema, who at least initially seemed unresponsive despite the nature of what was openly available.
This included highly sensitive data in fully editable states— the researchers were able to copy unencrypted fingerprint records and create new records in the database. That meant that the researchers could have walked into any of the “protected” premises and received a green light for full physical access.
While biometric security protection is often thought to be an unimpeachable cybersecurity method, when it’s deployed on its own (not as part of a multi-factor authentication system) it can leave physical and digital installations highly susceptible. And unlike changing one’s password from “abcd1234” (of which vpnMentor found plenty of examples), altering one’s face and fingerprints is slightly more time-consuming and a lot more painful.
Cybersecurity companies
Suprema is ranked among one of the world’s 50 largest security providers, and its clients include many members of the great and good of lists like the Fortune 500. It holds the largest market share in EMEA, though it does operate in dozens of countries worldwide. Users of BioStar 2 are advised to contact Suprema as soon as possible, and change administration dashboard usernames and passwords immediately.
While there is no evidence at present that shows the data was seconded by hackers, the incident should go to show that employing even a class-leader in the cybersecurity field is not an absolute guarantee of watertight protection technology. Additionally, the contents and nature of the database discovered by the benign researchers also point to levels of security practices that are charitably described as “low” among some BioStar 2 clients, and “dubious” at Suprema.








