‘Minute’ power fluctuations could reveal IoT malware
As the price of technology falls and interconnected devices become everyday normality, the security considerations surrounding IoT and IIoT are becoming more apparent.
Even those devices with SoC technologies (system-on-chip) are not immune, as micro-architectural attacks like Spectre and Meltdown can take advantage of hardware that’s not sufficiently protected.
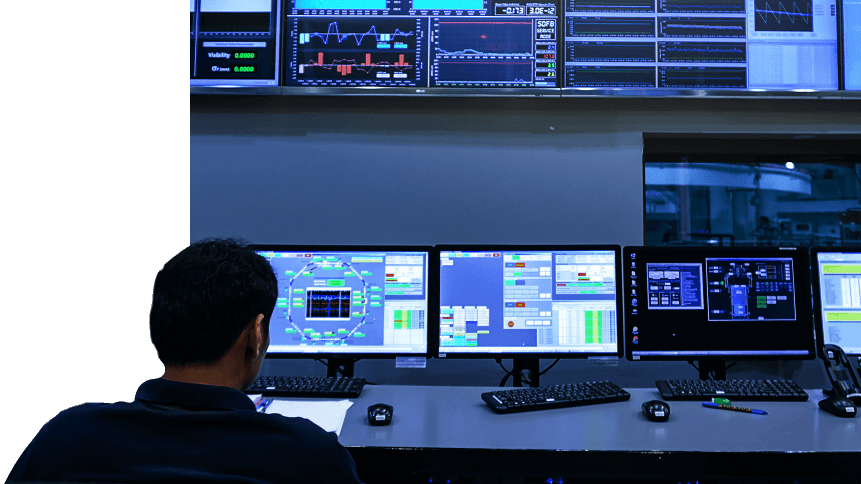
That sort of issue comes on top of new tranches of IIoT management solutions arriving on-stream that can also utilize previously isolated IIoT technologies and older OT (operational technology) communications protocols. These legacy systems are particularly vulnerable, as they were never designed to habit the same networks as the internet, where dangers a-plenty lurk.
Researchers from Carolina State University and the University of Texas at Austin have developed a new technique, however, that may help detect micro-architectural malware. By measuring power consumption patterns of healthy devices, an infected item’s minute power fluctuations can be used to betray the presence of (if not identify) a piece of malicious code, Science Daily reports.
“Embedded systems are basically any computer that doesn’t have a physical keyboard — from smartphones to Internet of Things devices,” said Aydin Aysu, co-author of the paper. “Embedded systems are used in everything from the voice-activated virtual assistants in our homes to industrial control systems like those used in power plants. And malware that targets those systems can be used to seize control of these systems or to steal information.”
For existing systems, third-party devices dedicated to monitoring power use will be required, but the technology could be built into future battery and/or power supplies. But smart batteries and the like are one thing; what about smart malware, capable of mimicking “normal” power consumption but continuing malicious activities?
In that instance, the team found that the malware had to throttle its own behavior to avoid detection, by up to 80 percent.
“In short, our approach can still reduce the effects of malware, even in those few instances where the malware is not detected […] This paper demonstrates a proof of concept. We think it offers an exciting new approach for addressing a widespread security challenge,” Aysu said.
Top 10 things you need to know about #IoT attacks via @mikequindazzi @Fisher85M#Infographic #CyberSecurity #infosec #Security #DDoS #BigData #DataScience #antivirus #Hacking #Firewall #tech #data #Cyberattack #databreach #artificialintelligence #iot #infographics #BigData pic.twitter.com/RmsDnEuPHo
— Devin Cleary (@DevCleary) May 14, 2019
The paper was presented during the IEEE International Symposium on Hardware-Oriented Security and Trust (HOST), its public debut. It came alongside reports on IoT specialist Bitdefender’s blog detailing the ease with which some IoT devices are compromised. According to the post, a personal alarm and tracker used by multiple manufacturers (see below) can be reset, betray its location, or have its microphone turned on by merely sending an SMS to the SIM card in the device.
While the devices do have some degree of protection (a PIN), the reset command, sent by malicious actors, will clear the device and make it ready for an incursion. The re-badged device is common in the US, the UK, and across Europe. Researchers at Fidus Information Security found the flaws, naming several affected devices currently on sale in the UK and further afield, which include:
- Pebbell 2 – HoIP Telecom
- Personal Alarm & GPS Tracker with Fall Alert – Unforgettable
- Footprint – Anywhere Care
- GPS Tracker – Fall Alarm – Amazon/Tracker Expert
- SureSafeGO 24/7 Connect ‘Anywhere’ Alarm – SureSafe
- Ti-Voice – TrackIt24/7