What can we learn from Visma’s cybersecurity breach?
When it comes to cybersecurity, every business from small, medium to large entities are under threat from a multitude of attacks.
Whether ransomware, cryptomining or otherwise, these tend to have financial motivations, so you might be forgiven for underestimating the influence of foreign politics on your defences.
According to Reuters, hackers working on behalf of Chinese intelligence breached the network of Norwegian software firm Visma to steal secrets from its clients. The company has used the attempted attack to urge other businesses of the importance of early detection.
An executive for the firm described the attack as potentially catastrophic. According to cybersecurity firm Recorded Future which probed the attack with Visma, the attack was part of a global hacking campaign by China’s Ministry of State Security, dubbed ‘Cloudhopper’.
Cybersecurity firms have warned of the campaign since campaign since 2017, and while none of the previously compromised companies have been disclosed before Visma, attacks have been targeted technology service and software providers in order to reach their clients.
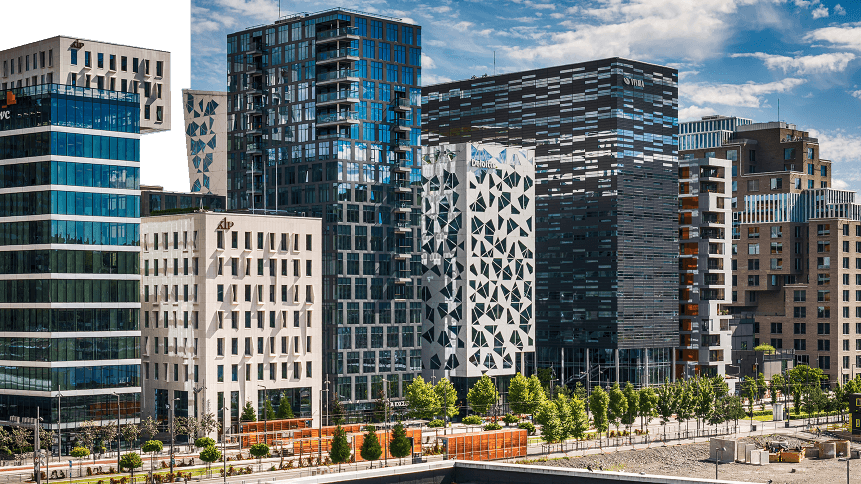
Visma, which reported global revenues of US$1.3 billion last year, provides business software products to more than 900,000 companies across Scandinavia and parts of Europe.
Espen Johansen, the company’s operations and security manager, said the attack was detected shortly after the hackers infiltrated the company’s systems and was confident that no client networks were accessed.
“[…] if I put on my paranoia hat, this could have been catastrophic,” he said. “If you are a big intelligence agency somewhere in the world and you want to harvest as much information as possible, you, of course, go for the convergence points, it’s a given fact.
“I’m aware that we do have clients which are very interesting for nation-states,” he said, declining to name any specific customers.
Johansen said that his team discovered the hackers quickly and “didn’t get more than a day or two, max”, before action was taken. He said that it was “utterly essential” to catch hackers early and prevent them from having more time inside a system.
Visma has credited the encryption of all employees passwords as providing a line of defense that slowed the attack: “The biggest problem with such players (hackers), is when they get enough time on the inside without being discovered.”
Paul Chichester, director for operations at UK’s National Cyber Security Center, said that this case highlighted the dangers from cyber-attacks on a company’s supply chain.
“Because organizations are focused on improving their own cybersecurity, we are seeing an increase in activity targeting supply chains as actors try to find other ways in,” he said.
In a report by Recorded Future, it says the attackers gained initial access to the Visma network around August 17 of 2018.
YOU MIGHT LIKE

Should we ‘name and shame’ cybersecurity shirkers?
An examination of the network logs revealed an employee’s credentials were stolen and used to authenticate to the network outside of this individual’s working hours.
It is speculated that the Tianjin State Security Bureau, which is a regional arm of the Ministry of State Security could be behind the attack.
Throughout August 2018, the APT10 actors regularly logged into the Visma network via accessible Citrix servers using two valid user accounts. The times of the logins were consistent with a GMT+8 time zone, indicative of typical Tianjin, China working hours.
Priscilla Moriuchi, director of strategic threat development at Recorded Future said the hackers’ activity inside Visma’s network suggested they intended to infiltrate client systems in search of commercially-sensitive information.
“We believe that APT 10, in this case, exploited Visma networks to enable secondary operations against Visma’s customers, not necessarily to steal Visma’s own intellectual property,” she said.
“Because they caught it early, they were able to discourage and prevent those secondary attacks.”
Recent research by eSecurity Planet found that around one-third of organizations are unprepared for a cyberattack, with regular penetration testing— where trials are carried out to seek vulnerabilities— were neglected among 40 percent of businesses and 60 percent of companies with fewer than 100 employees.
The same report found that just 40 percent of smaller organizations are involved in threat hunting one a year or more, whereby companies proactively and iteratively search through networks to detect and isolate advanced threats that evade existing solutions.









