Know How, What, Where and When in API Traffic: Sentinet Steps Up
A significant trend in business technology over the last few years has been the replacement of large, monolithic ERP (enterprise resource planning) applications with dedicated point products, linked by APIs. Specialist applications can offer significant advantages for end-users, not least of which is a more open structure with regards to interoperability with the rest of the technology stack.
Many organizations prefer to use multiple point products over a monolithic ERP because internal data flows inside a large proprietary platform are not necessarily observable or configurable.
That’s not to say that ERP companies offer a poor choice for many businesses – companies like SAP and Salesforce are not household names by accident. Rather, when companies begin to link point products by APIs and start to automate those links (with software like RPA [robotic process automation]), the full power of the software stack begins to realize a significant ROI.
However, linking internal software instances via APIs is one thing; it’s quite another to allow third-party access to critical parts of a company’s infrastructure, even when very carefully overseen. Interfacing with partners and services outside the company can mean directly exposing resources to public IP spaces, and so needs careful management – and not just from a security standpoint. Exposing internal resources to the outside world may be essential in today’s ultra-connected business environments, but it can place new loads onto APIs, the software behind them, and all the enterprise’s digital systems.
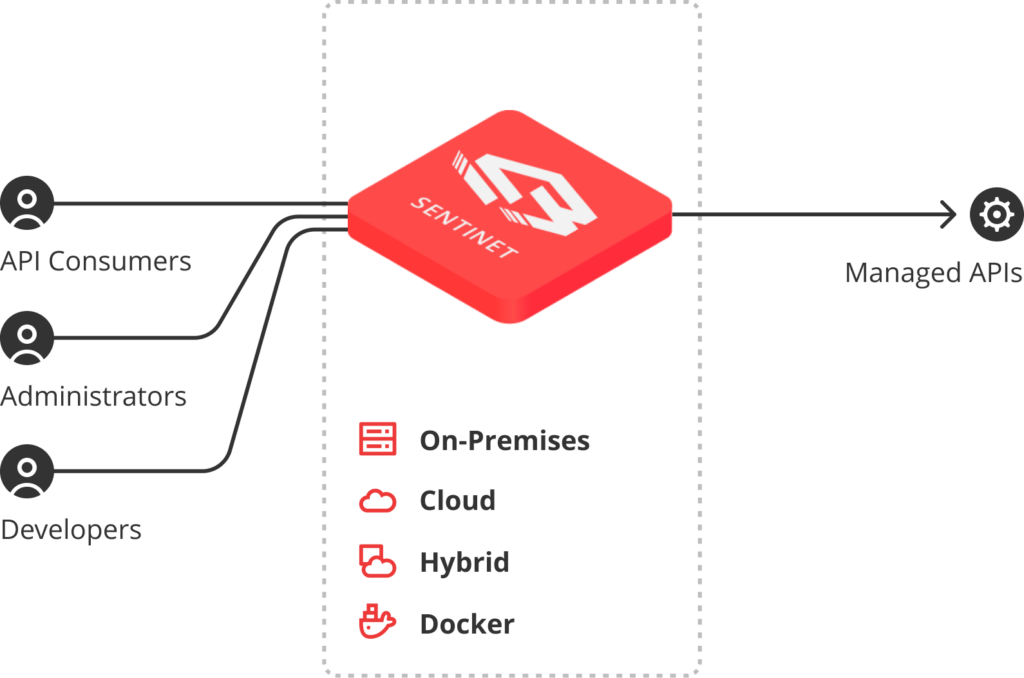
Creating these structures on which connected businesses operate needs proper API Management right across all systems and a gateway to negotiate, oversee and control external access, and arbitrate between internal and external API traffic. API oversight can help prevent misuse or overuse of resources by less important processes and, for example, bolster security, help RPA deployments work better, give insights into what procurement plans should be, and where the company needs to dedicate more resources.
The Sentinet API Management platform from Nevatech addresses these challenges by offering tight connections between traditional security enforcement measures and active monitoring of internal and external API traffic. It can instigate or flag the need for system responses, inform administrators who or what is accessing every API in the complete IT stack, and help troubleshoot APIs’ function and overall performance. The data it collects can be used to build real-time snapshots of API activity and produce reports on historical data to show API use and visualize behaviors for analysis from anywhere in the enterprise.
The Sentinet platform offers the kind of fine-grained privilege and access controls you would expect, too, including must-have features like API key expiry control and fine-grained authorization rules (using X.509 certificates, OAuth/OpenID Connect schemas, or username and password).
Depending on where you read it, API traffic on the internet as a whole comprises between 40% and 60% of total packets by volume. In whatever case, APIs are significant in any enterprise. Ensuring trouble-free performance of every interface is of paramount importance, so troubleshooting APIs’ functional problems and observing performance execution metrics are essentials to maintain the organization’s operations.
The same statistics regarding traffic quantities also highlight another of the Sentinet platform’s stand-out features: the ability to provide the necessary flexibility to control when to record API data, how much, and what precisely to record. As well as the overall volume – even warnings-only logging levels will quickly fill available space – there is often private information that needs to be obfuscated or removed from the recorded logs. Sentinet provides this capability yet retains the vital information systems administrators and security personnel need: information directly relevant to API performance and security
To learn more about this increasingly vital element of both the security stack and business operations, get in touch with a technical specialist from Nevatech who will be able to answer your specific queries.









