Ultra-secure mobile comms just took a giant leap forward: the Bittium Tough Mobile 2
The company behind the Android operating system, Google, is in the business of data.
It’s not surprising, therefore, that the operating system that runs the majority of the world’s smartphones is not particularly secure — after all, Android software is designed to be as open as possible so it can run on as many handsets as it can. In recent years, concerns about data security have meant that Google itself, and many other companies, are producing apps or system add-ons to attempt to screw the lid down on what’s a reasonably insecure means of communication and data interchange.
Clearly, if a member of staff or high-ranking executive loses their phone, or accidentally sends sensitive data to the wrong party, there’s little that any third-party security features can do to ameliorate the consequences, other than remotely wiping the phone — and that’s not always possible. But over and above that seemingly unavoidable occurrence, most companies and organizations let their employees freely mix their personal lives with their work role. That’s epitomized in BYOD policies, where personal Dropbox apps share the same platform as the company’s most valuable IP. Most phones in the enterprise are a recipe for disaster, and a disaster that indubitably will happen, not one that just might.
Addressing this reality is Bittium, a Finnish company with a long track record in secure military communications methods, safe practices, and rock-solid hardware and software. Building on its market position, too, in the smartphone space, it’s begun taking orders for its Tough Mobile 2, a bespoke handset that puts security first— in literally every aspect of the modern smartphone. If your company or organization values its data and its privacy (or the privacy of your clients), then this specialist company’s offerings must be top of your list for your secure smartphone needs.
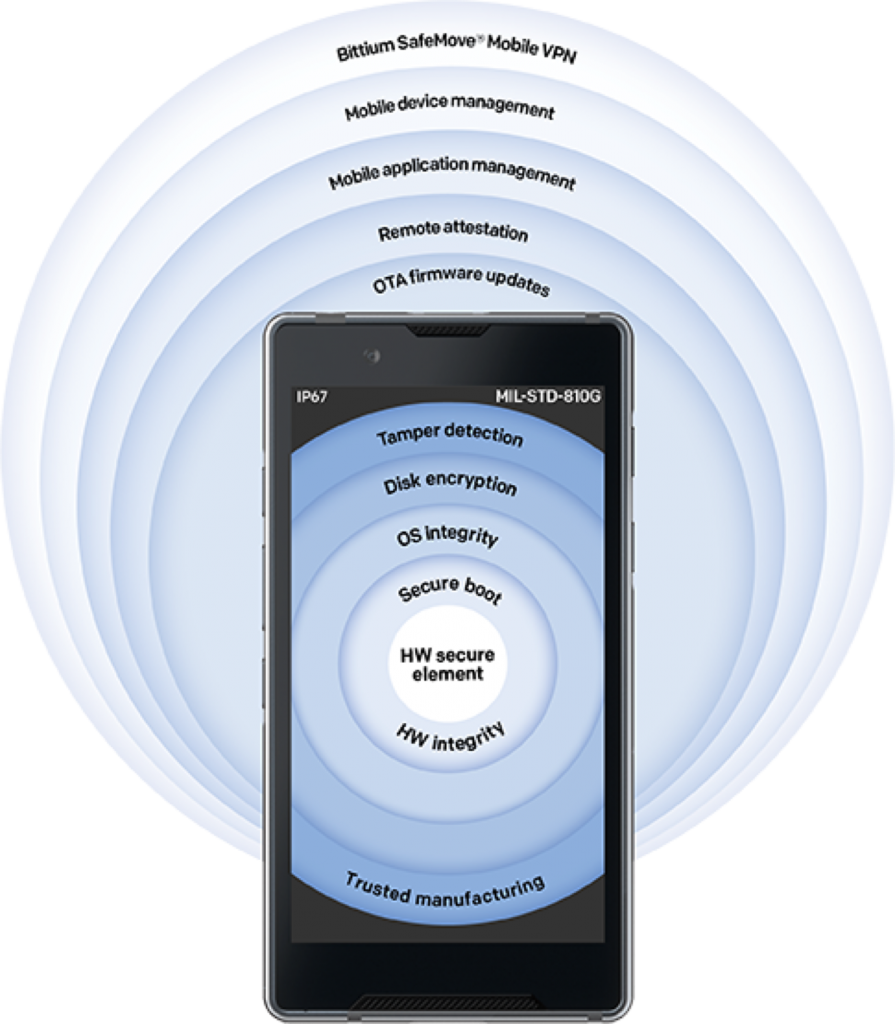
Source: Bittium Secure Suite
Software safety
The Bittium Tough Mobile 2 behaves to all intents and purposes like a stock Android handset (and looks like a rather smart, high-end model, as well), with apps, icons, settings and even access to the Google Play Store (if required). The phone runs a hardened version of Android 9 (Pie). That means staff will be able to pick up this handset and use it straight away; it’s not an esoteric piece of military equipment. But there are significant details under the surface that make this Android variant the safest currently available mobile operating system.
The phone can communicate via an always-on VPN, so all data in transit is encrypted. Regardless, all data stored on the device (including any added SSD card) is encrypted at rest, as you’d expect. The twin SIM phone can also communicate just about anywhere in the world, as it “speaks” every variation in service radio frequencies around the globe.
It’s simply impossible for users to get around the encryption applied at rest or in transit: there’s no ADB connectivity, users can’t “root” their handset, and each instance can be configured remotely by Bittium’s Secure Suite. That’s an MDM (mobile device management) platform that can push updates, pull use stats, shut down and wipe the handset, and even check that every handset is in the same state (physically and virtually) as it was when it left the Bittium factory.
For organizations with an MDM already in place, or legacy software still in use, there’s a Secure Push API, and Secure Suite will happily add much-needed security hardening capabilities to any third-party MDM.
End-users can switch between compartmentalized profiles or Workspaces, meaning that the phone can remain a personalized device suitable for leisure use, but then be switched to being a secure work device. Multiple Workspaces can be configured to any level of security, with only the most secure apps enabled, and even Google Play API services shut down, so there’s no tracking whatsoever on the device (and to gain the notable boost to battery life turning off that facility invariably brings, too).
Hardened hardware
Speaking of battery life, the Bittium Tough Mobile 2 also has an internal backup battery, to maintain the device’s security standards and ensure tamper detection systems remain active, even when the phone’s “dead.”
Bittium is rightly proud that it designs and builds its phones in Finland, giving complete oversight over every aspect of engineering and component quality. There are physical anti-tamper hardware devices built-in, so the phone will destroy all information if the case is opened; similarly, the device isn’t susceptible to cryogenic freezing or power-glitch attacks. There’s a dedicated chipset that runs secure keys and provides encryption and authentication, which makes the security features in this Android phone impossible to alter or turn off in software, making it immune from unauthorized users’ or attackers’ best efforts to reveal its secrets.
There are several configurable hardware buttons that perform programmable actions like putting the device into immediate privacy mode (no microphone, Bluetooth, or cameras), or acting as a software-defined emergency button.
Its final surprise is the price tag — as technology journalists, we’ve seen handset prices rise over the last ten years, with folding phones and Apple’s latest models easily hitting the $1500 mark for feature sets that are frankly dubious, especially for business-oriented users, or the security conscious. But at a price of €1550 (US$1729, UK£1330, AUD$2515), the Bittium Tough Mobile 2 won’t even raise an eyebrow in the Procurement Department.
With data now demonstrably one of the world’s most valuable commodities, companies and organizations that value data privacy and security should be paying attention to Bittium. After all, a phone company based in Finland shouldn’t come as much of a surprise, but Bittium’s advanced security stack offers the best chance of no unpleasant surprises down the line, from any level of your organization’s user base.
Get in touch with a representative from Bittium today, or download a specification sheet (PDF) for the Bittium Tough Mobile 2 to see what security standards the company maintains, and usually exceeds. Recommended.









